Phishing is no longer an annoyance for organizations that are concerned with the security of their systems. Rather, phishing is a systems problem 2026 that is designed to challenge the ability of an organization to work on a large scale. Phishing happens faster, is targeted, and is not easily detectable in the future, 2026, where the scammers do not simply send out general phishing emails. Instead, they are monitoring the systems to know the appropriate time to strike.
Meanwhile, the trend of phishing in 2026 reveals the move towards the concept of precision. Phishing is contextual and uses the techniques of trust. So, it does not depend or rely on the concepts of volume, credibility, and power. So, the traditional remedy is not effective.
This article not only helps understand how these new tactics are generated, how good this approach is likely to be, and how these tactics should ideally be defended against. On a more important level, this article also helps understand how these tactics should ideally be defended against, how technology, processes, and people should work together.
Why Phishing Attacks in 2026 Look Fundamentally Different
Phishing no longer works by simply flooding inboxes with lousy grammar bait. In phishing attacks 2026, scale comes from precision. Attackers do their homework on roles, relationships, and routines well before hitting Send. Emails now arrive with the right tone, at the right moment, and with context that is believable.
Instead of generic warnings or fake promotions, today's attackers construct messages that resemble actual business activity. An invoice arrives right after a meeting. A login alert follows a legitimate password reset. Because these lures reflect ongoing workflows, users demur less. Even trained employees may act before they think.
Meanwhile, next-generation phishing methods are deeply dependent upon context awareness. Modern attacks pull signals from breached inboxes, public profiles, and prior conversations. Each message, consequently, is representative of internal language, familiar senders, and expected actions. This shift removes many of the red flags that legacy security tools were designed to detect.
Consequently, modern phishing attacks evade traditional filters with ease. Signature-based systems look for known patterns, not subtle anomalies. Keyword scanning fails when language is natural and varied. Moreover, AI-generated text constantly mutates, which prevents reliable fingerprinting.
However, the most important change is structural. Phishing is no longer a single malicious email to block. Instead, it is a sequence of interactions designed to guide behavior over time. Because of this evolution, defenses must move beyond spam prevention and focus on behavior, context, and risk propagation across systems.
Emerging Phishing Tactics Defining 2026
AI-Powered Phishing at Scale
AI-powered phishing has moved from experimentation to industrial use. Attackers depend on large language models now for generating emails that sound natural, confident, and situationally aware. Unlike older templates, these messages tailor tone, vocabulary, and structure to that of the recipient's role. A finance manager gets precise payment language, while a developer sees technical phrasing that feels internal.
In addition, there is multilingual targeting, which, without requiring extra work, AI can accomplish. Campaigns get to switch languages effortlessly according to geography or past correspondence. In this way, capability allows attackers to scale globally while maintaining local credibility. Organizations, therefore, cannot depend on language errors as warning signs anymore.
Another defining characteristic is constant message evolution. Every email is slightly unique, even with the same campaign. Sentence structure, phrasing, and intent cues are in constant change. With this, pattern-based detection can barely keep up. These advanced phishing techniques are not static payloads but adaptive systems.
Importantly, AI also optimizes timing and follow-ups. Messages are resent, reframed, or escalated based on user behavior. If no response arrives, a reminder appears. If a reply comes, the conversation continues naturally. Therefore, phishing becomes a dialogue rather than a single event, which increases success rates while evading traditional controls.
Deepfake Impersonation and Synthetic Trust Attacks
Deepfake is the new class of impersonation attacks based on synthetic trust. Indeed, a voice clone can realistically mimic the tone, cadence, and emotions of the target. Meanwhile, a series of short videos can be used to stage executives/vendors asking for something. This creates a shift in phishing from link/attachment-based attacks to persuasion attacks in general.
Instead of sending malware, attackers use their position of power and familiarity. One can create a voice note asking the person to hurry up or even send a video to confirm the transaction. Because it sounds like internal communication, the customers concentrate on the compliance rather than checking the message.
Such identity-driven attacks are particularly effective against finance teams and leadership groups. Their attack surface is no longer the physical device. As deepfake tools improve, it becomes increasingly difficult to identify them without some form of second-factor verification. Organizations' assumptions about "genuine" dialogue must be reconsidered.
Business Email Compromise (BEC) Becomes Harder to Detect
Business Email Compromise (BEC) – This threat evolves beyond simple email spoofing. When receiving business email compromises in 2026, the following behaviors are expected: In 2026, attackers generally have lasting access to an inbox, listening in on conversations before acting.
Once the attacker is in a position, they hijack active threads rather than creating new ones. A real conversation will suddenly contain a small modification to the details of the payment. Due to the authenticity of the information, the people in question will rarely question the request. These new types of phishing attacks are based on familiarity.
The targets are still payment diversion and invoice fraud, but with greater precision. The timing is also more accurate, as messages are transmitted when expected, sometimes even mentioning previous communication. The obvious red flags are no longer present, so BEC is identified based on behavioral changes rather than sender and domain reputation.
Multi-Channel Phishing Campaigns
Phishing attacks are increasingly being carried out through multiple communication mediums. Email is used to set up the context, while SMS is used to create a sense of urgency, and voice is used to take final action. This is a blend of smishing, vishing, and emailing. When evaluated in individual scenarios, they appear logical.
Typically, attackers create a pretext over time. First, an email sets a context. Next, a message verifies the status. After that, a call attempts to prompt a quick reaction. These social-engineering techniques take advantage of the expectation of high levels of responsiveness and consistency.
Due to this channelization, attack vectors are targeted between these isolated groups. A message might have been detected in one channel but could be innocuous in another. To address this major problem, there is a need to consider phishing as a multi-touch process.
Why Traditional Anti-Phishing Solutions Are Falling Behind
Conventional anti-phishing tools have been built with a different threat model in mind. They anticipate a threat model that is static, repetitive, and identifiable for phishing attacks. In the year 2026, this threat model is not as applicable. In the past year, phishing attacks have become personalized to the user and seem to be indistinguishable from genuine messages.
Another important weakness which signature-based systems struggle to efficiently address is that the approach seeks to identify patterns of repetition, suspicious connections, or suspicious senders. Nevertheless, the content of the emails created by the AI can change frequently in their layout and wording. Once the content starts to change, as it will because the content of the message will always be distinct, many of the malicious emails will not be flagged as suspicious by the systems.
Additionally, there is an increase in “alert fatigue” in organizations. This is due to the vast number of alerts that are sent by modern email filters, with a majority of these being false positives. This makes it hard to respond as people are flooded by alerts, while others have also become immune to these alerts, causing them to ignore these security notifications altogether.
User reporting introduces another limitation. While training helps, it places responsibility on individuals during moments of urgency. Attackers exploit this pressure deliberately. Moreover, not all users report suspicious messages consistently. Therefore, relying on manual reporting leaves gaps that attackers can exploit.
Finally, many phishing detection methods operate in isolation. They evaluate emails without understanding broader context, intent, or downstream impact. Because phishing now unfolds as a process, not a single event, defenses must evolve. Effective protection requires coordinated detection, behavioral analysis, architectural safeguards, and stronger controls around Encrypted Email to reduce content exposure even when accounts are compromised.
How to Defend Against Phishing Attacks in 2026 at Scale
Modern Phishing Detection Methods
Defending against these attacks must move beyond traditional static rules, which change to adaptive analysis. Organizations must shift from asking whether an email looks suspicious to asking whether behavior deviates from normal patterns. Behavioral analysis emphasizes the flow of actions, replies, and responses towards an email.
Inspection is equally central. The detection systems carry out evaluation in relation to who is communicating, what the relationship is between them, and whether it aligns with recent activities. A payment request that does not flow through normal approval patterns could be suspicious even if sent in an appropriate message. The context is equally significant.
Anomaly detection adds strength to the above mentioned phishing detection techniques. For instance, anomalous changes in tone, timing, and type of requests may be indicative of system compromises. Systems that successfully identify such anomalies across users and workflows are capable of detecting attacks that otherwise go unnoticed by signatures. As phishing becomes even more conversational and flexible, so too must the detection.
Phishing Prevention Strategies That Scale
The implementation of effective policies for the prevention of phishing requires the use of identity-first security. Rather than trusting messages based on the sender's identity, the security system should verify the identity, intent, and authorization of the sender continuously to limit the risk of compromised credentials and impersonation attacks.
The zero trust assumptions for email are becoming more and more essential. In reality, every request with credentials, payment information, and/or sensitive information must engage a second level validation approach. Therefore, this approach is becoming much less effective, as is the previous practice. Such practices are becoming consistent with modern email security practices that limit trust.
Controlling the "blast radius" is also significant. Segmentation stops the "avalanche effect" in the case of successful phishing campaigns. Access controls and approval mechanisms limit the "impact" reached by the perpetrating threat actors once they have gained a ''toehold'' in the enterprise environment.
Importantly, this enables scalable prevention to move responsibility away from individual users. Although training is important, systems should absorb most of the risk. This helps to eliminate reliance on perfect human behavior under high pressure.
Secure Email Infrastructure as a Defensive Layer
In the defense against phishing, architecture is very important. This is because a secure e-mail system reduces the risks by design as opposed to detection. The encryption limits access to privileged content, therefore providing limited space for the attackers in the event of detection.
This, in turn, also helps manage risks related to AI. Without protection, these emails cannot be used by any unauthorized AI, thereby controlling the risk in AI in a better way, especially when these AI tools become more common in communication.
Some organizations are beginning to prioritize privacy-first infrastructure as part of their long-term phishing resilience strategy. Instead of relying solely on detection, they look for platforms designed to limit data exposure by default. Atomic Mail is one example of this approach, focusing on encrypted communication and reduced internal data visibility as part of a broader architectural defense model. While no solution eliminates phishing entirely, embedding privacy at the infrastructure layer can significantly reduce the blast radius of compromised accounts.
Organizational Readiness: Why Humans Still Matter
Technology alone cannot eliminate phishing risk. Even the most advanced controls depend on how people respond under pressure. Therefore, organizational readiness remains a critical defense layer. The goal is not perfect awareness but consistent behavior that reduces exposure.
Traditional training often emphasizes recognition. Employees learn to spot suspicious links or unusual language. However, modern attacks rarely look suspicious. As a result, effective programs focus on behavior change rather than memorization. Clear rules about when to pause, verify, and escalate decisions matter more than identifying subtle clues.
Verification workflows operationalize human-in-the-loop security. Instead of leaving judgment to individuals, organizations define structured steps for sensitive actions. Payment requests, credential changes, and data exports should always trigger secondary checks. These checks shift responsibility from instinct to process.
Out-of-band confirmation is especially important for financial actions. A phone call, secure message, or separate approval channel can interrupt deception. While this adds friction, it significantly reduces fraud success rates. These fraud prevention workflows work because they break the attacker’s control over timing and narrative.
What Phishing Trends in 2026 Signal for the Future
The biggest takeaway from the phishing trends for the year 2026 is the concept of being adaptable. Gone are the days when the cyber attacker is only using one method or avenue. Now, he/she is constantly testing, making changes, and improving their campaigns. If their initial plan fails, others will emerge right after.
Trust exploitation will remain prevalent. Rather than attacking the systems, they compromise expectations, authority, and even routine operations. With emerging phishing techniques that mature further, deception feels less intrusive and more like legitimate business communication. This reduces uncertainty and streamlines decision-making in favor of the attacker.
At the same time, automation amplifies reach without sacrificing personalization. AI enables attackers to scale conversations while maintaining relevance. Therefore, future phishing will resemble customer engagement workflows more than traditional scams. Defenders must recognize this convergence to respond effectively.
These signs point to the importance of considering flexible and privacy-oriented defense solutions. Rigidity and increased data collection create unnecessary friction without improving the results. Organizations can actually benefit from solutions that change with natural behavioral changes while reducing unnecessary exposure of sensitive data.
Looking ahead, what’s important to future resilience is architecture just as much as detection. Security strategies that emphasize adaptability, context awareness, and respect for data boundaries will likely prove more resistant to the next chapter of phishing evolution.
Conclusion and Practical Takeaways
Phishing has grown to become an operation risk that is not limited to emails. In 2026, financial choices and operations are affected by this attack. When evaluating this issue, people should understand that combating phishing does not solely rely on technical controls but rather should be adopted as a business risk.
Effective defense relies on layers rather than single tools. Detection must adapt to behavior and context. Prevention should limit trust by default. Architecture needs to reduce exposure when failures occur. When these elements work together, organizations gain resilience instead of chasing individual threats.
Equally important, defenses must scale without increasing complexity for users. Clear workflows, verification steps, and privacy-aware systems help teams act safely under pressure. As communication tools become more intelligent, protecting sensitive data becomes part of the security strategy itself.
So, for an organization considering their email infrastructure foundation, an exploration of a privacy-first email infrastructure such as Atomic Mail could be a means to minimize unwarranted data exposure while enabling additional security mechanisms. At the end of the day, truly effective phishing defense comes from integrating technology, process, and architecture into a system that addresses the needs of today and tomorrow.
 Access Request Form
Access Request Form
 Afterparty RSVP Form
Afterparty RSVP Form
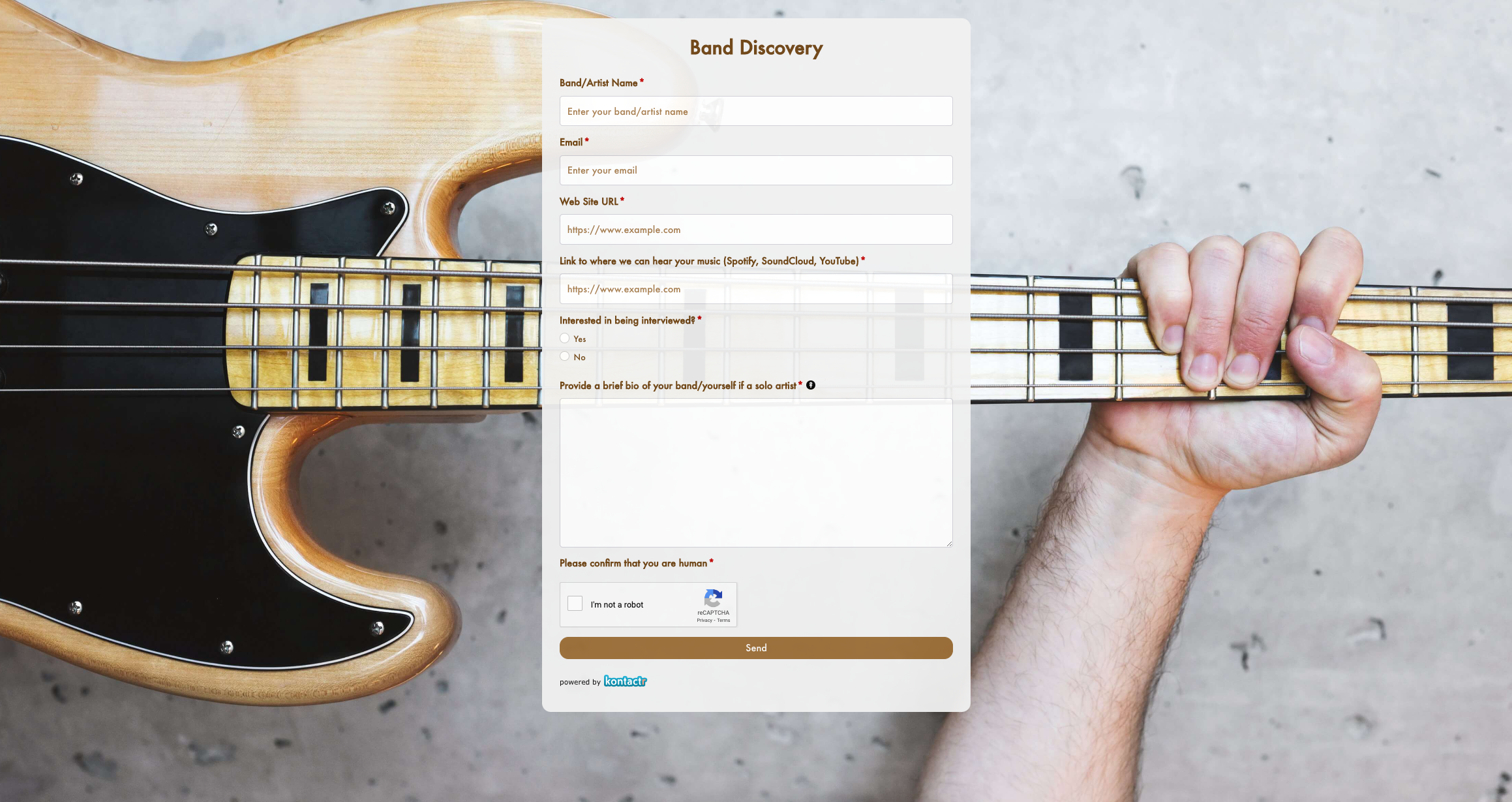 Band Discovery Form
Band Discovery Form
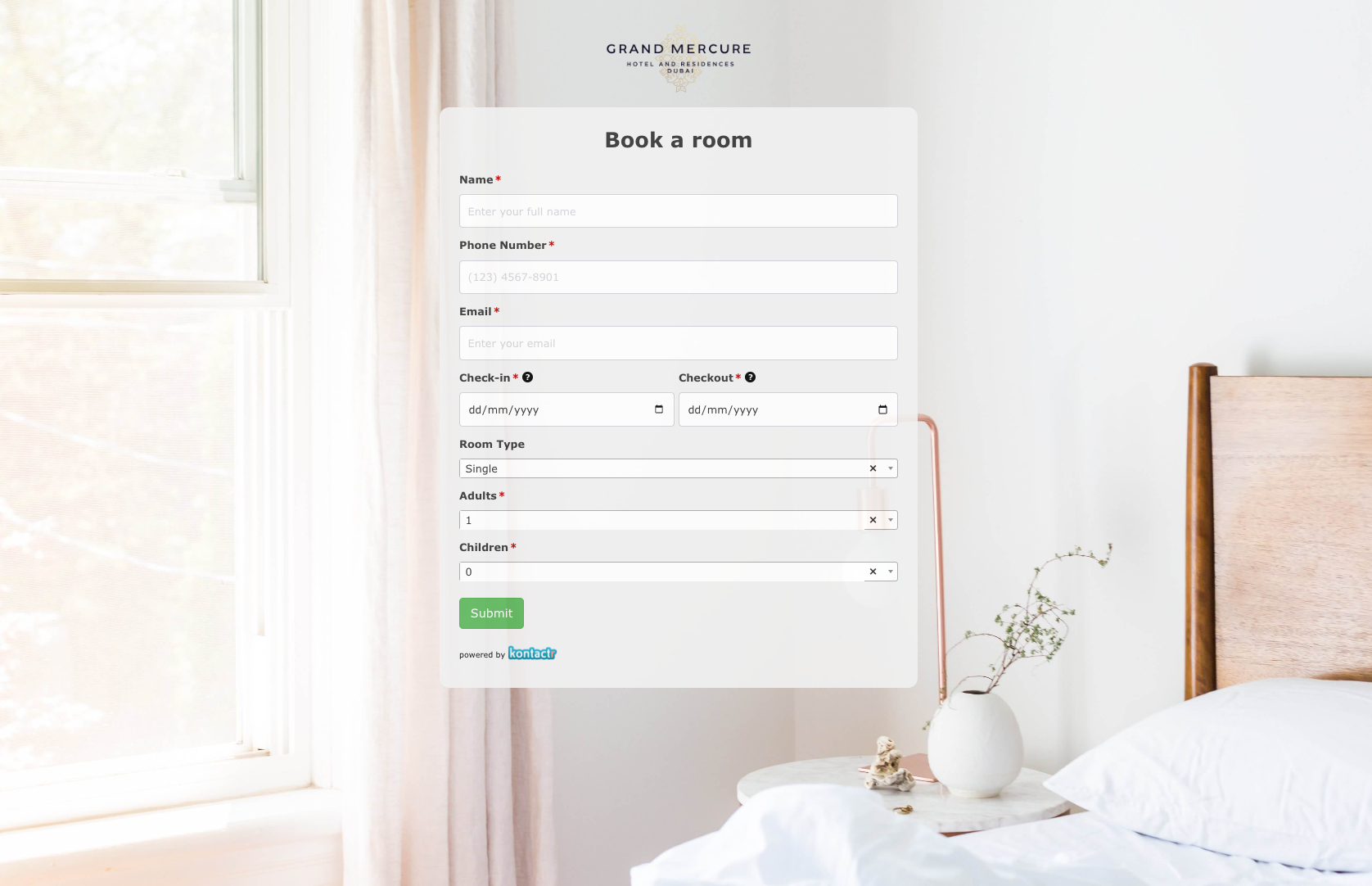 Book a room Form
Book a room Form
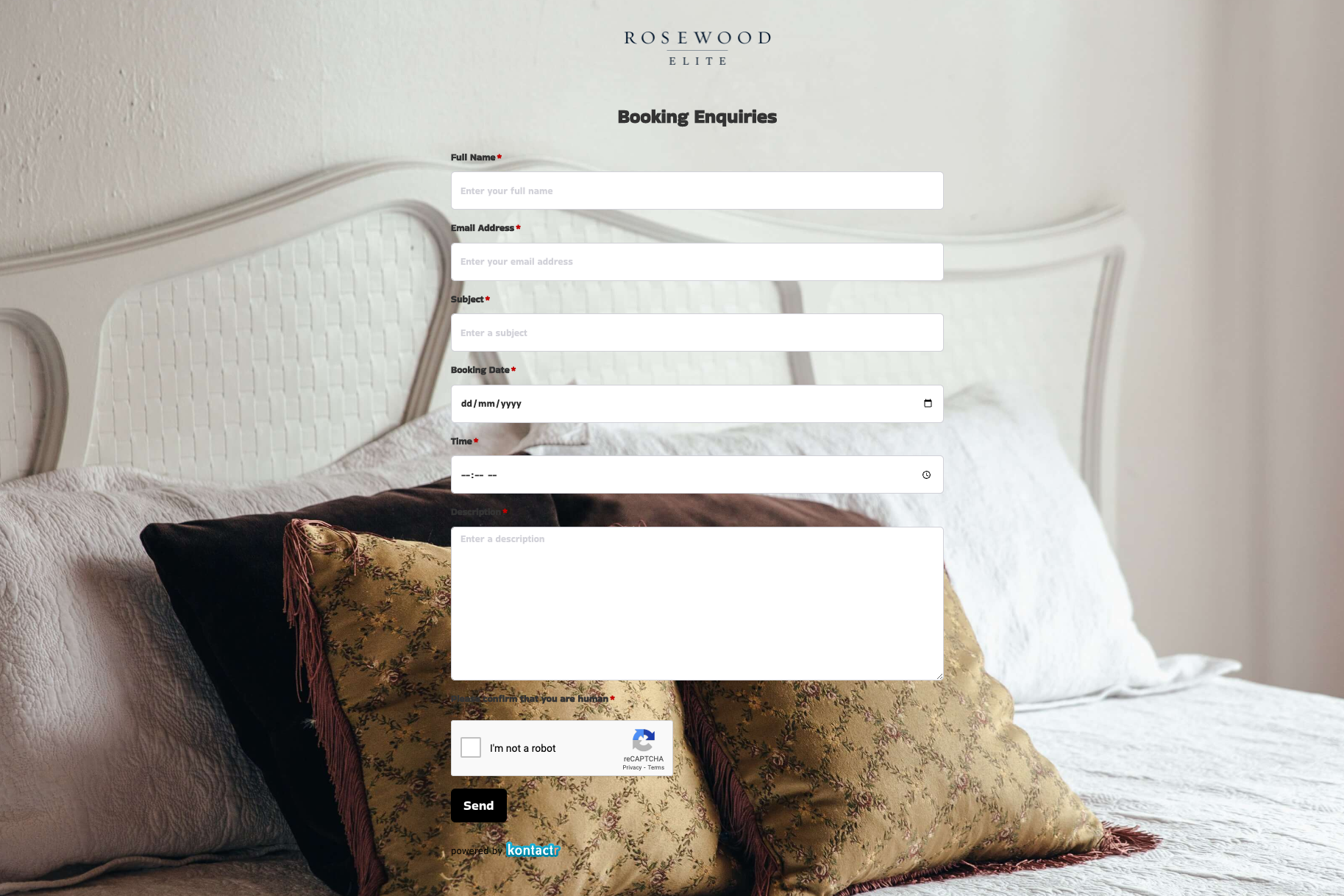 Booking Enquiries Form
Booking Enquiries Form
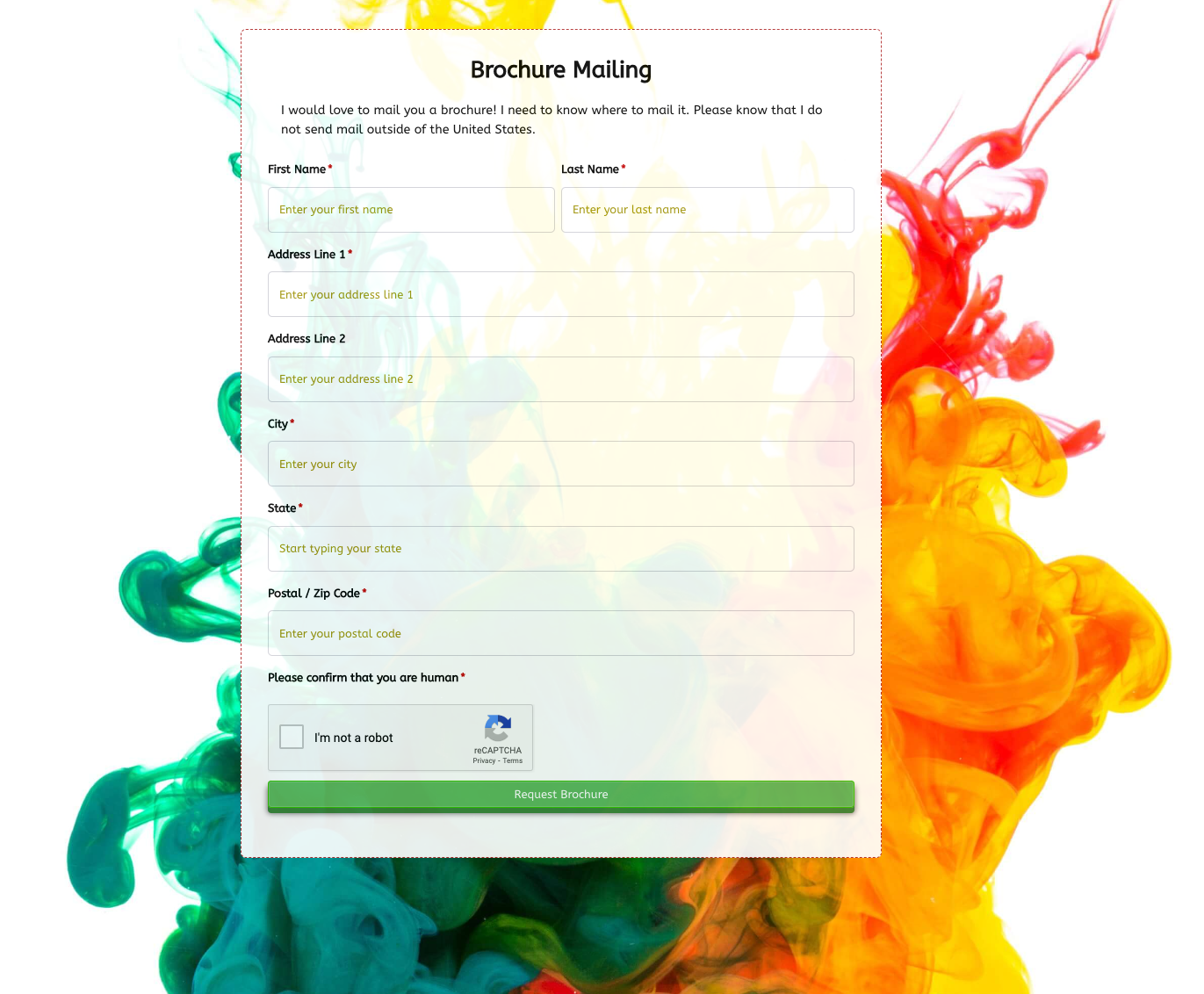 Brochure Mailing Form
Brochure Mailing Form
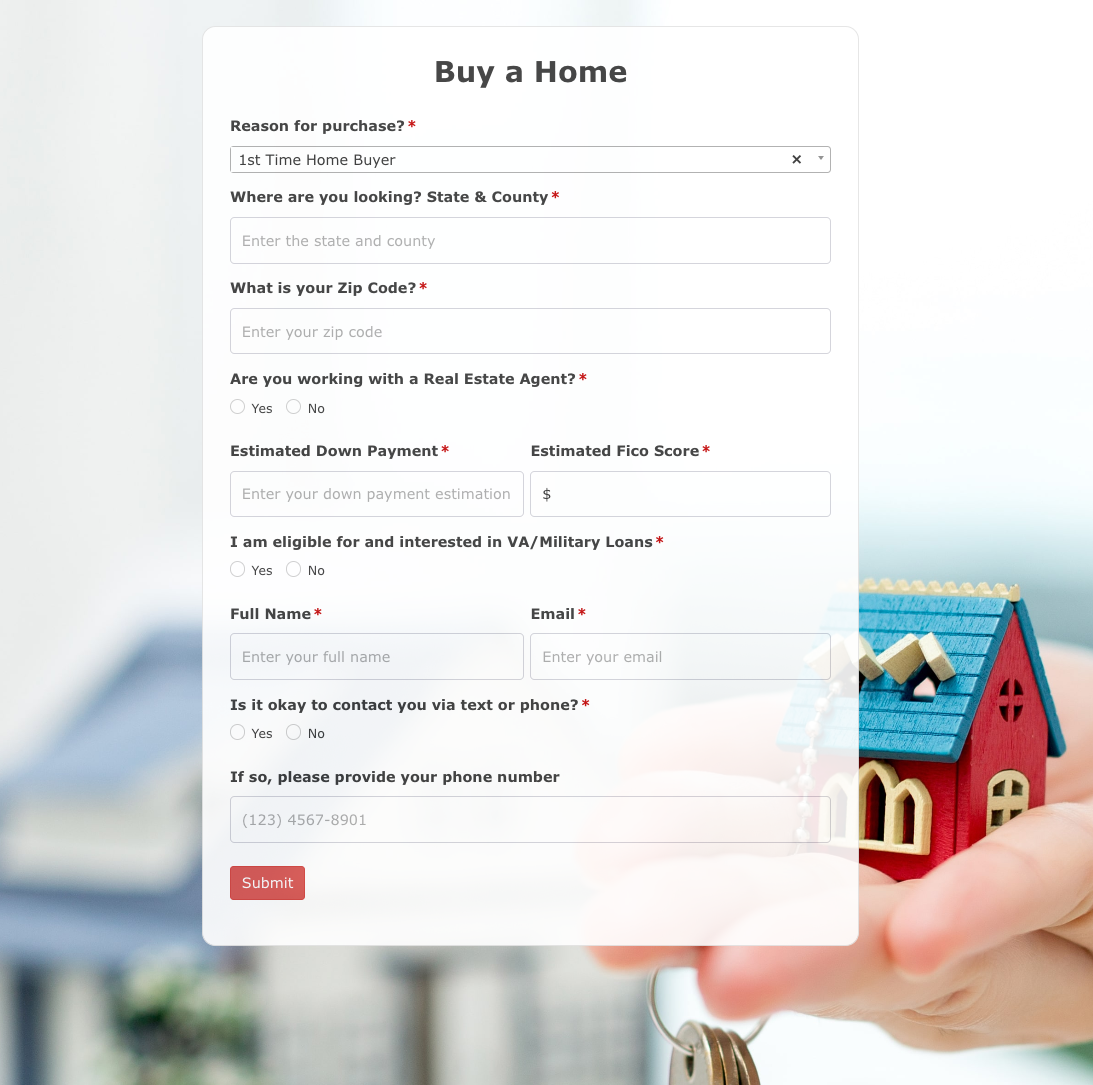 Buy a Home Form
Buy a Home Form
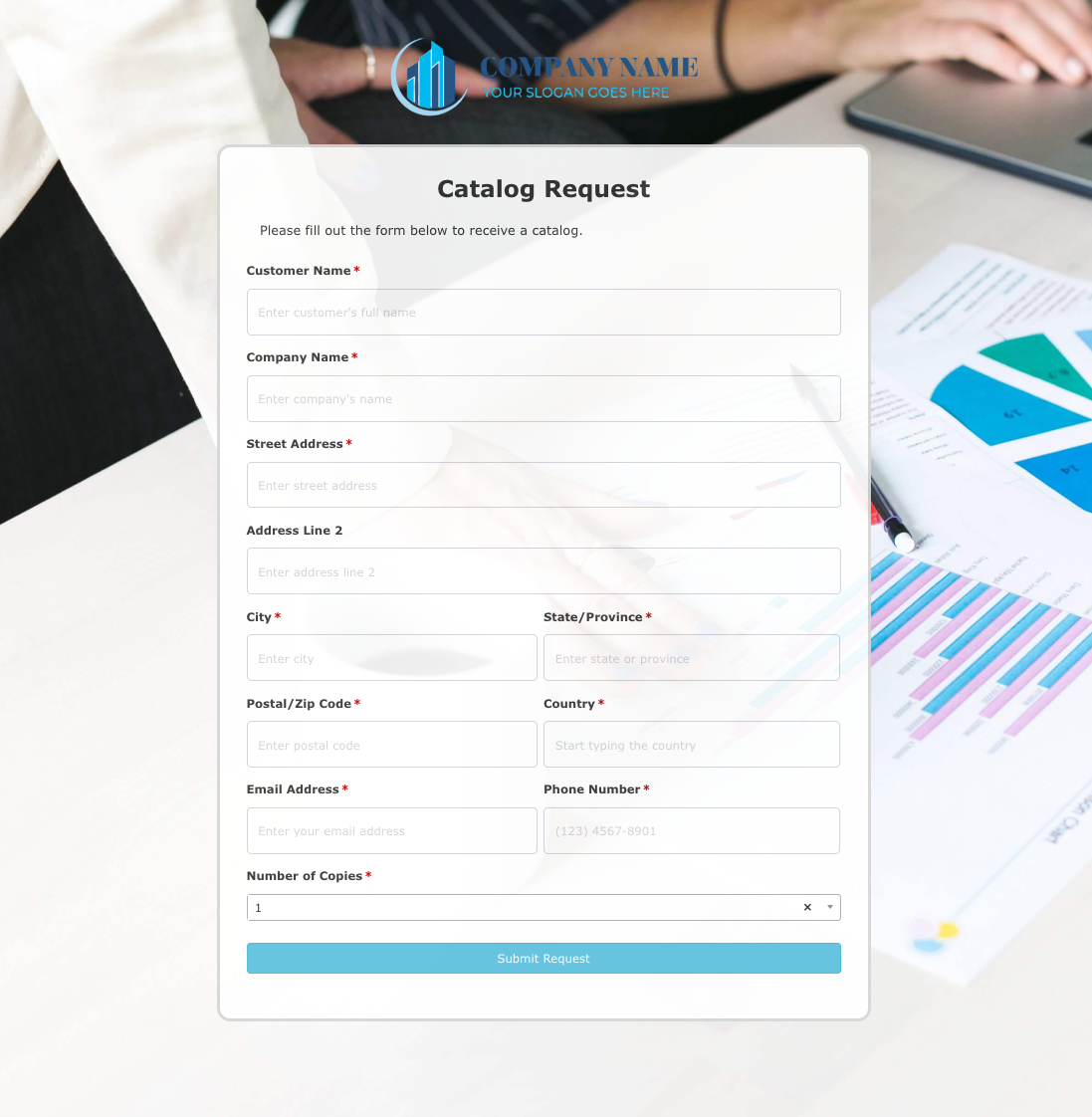 Catalog Request Form
Catalog Request Form
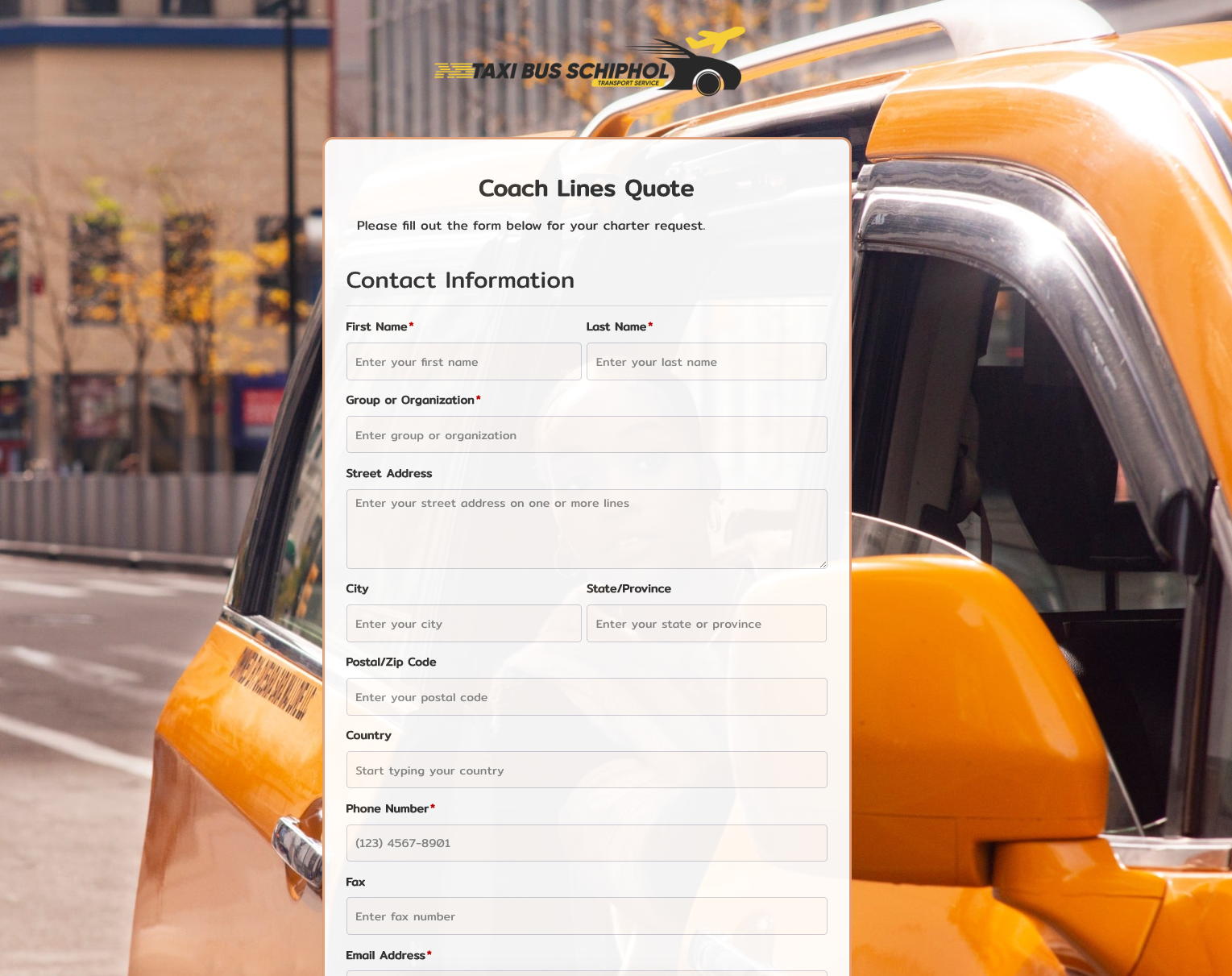 Coach Lines Quote Form
Coach Lines Quote Form
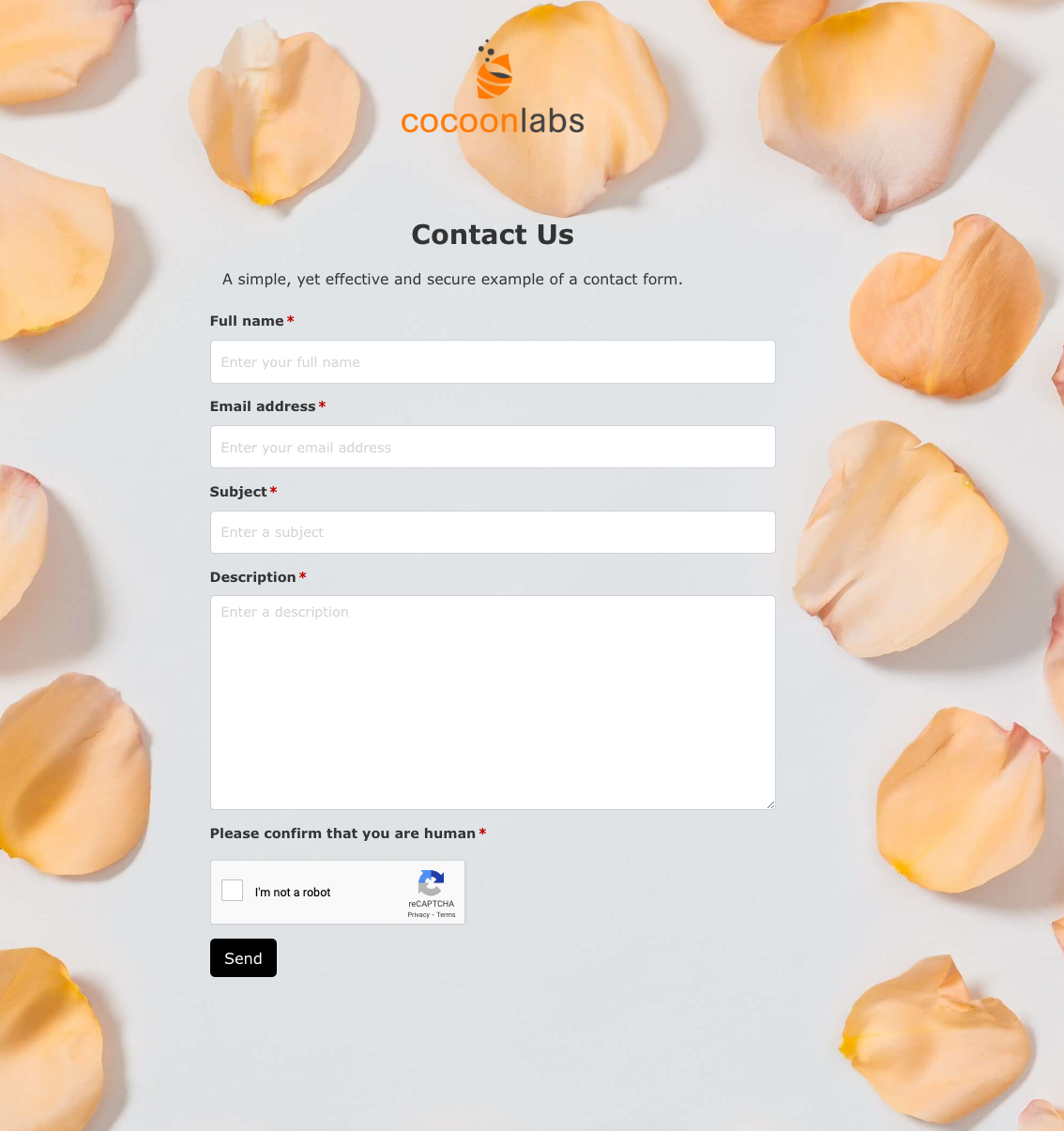 Contact Us Form
Contact Us Form
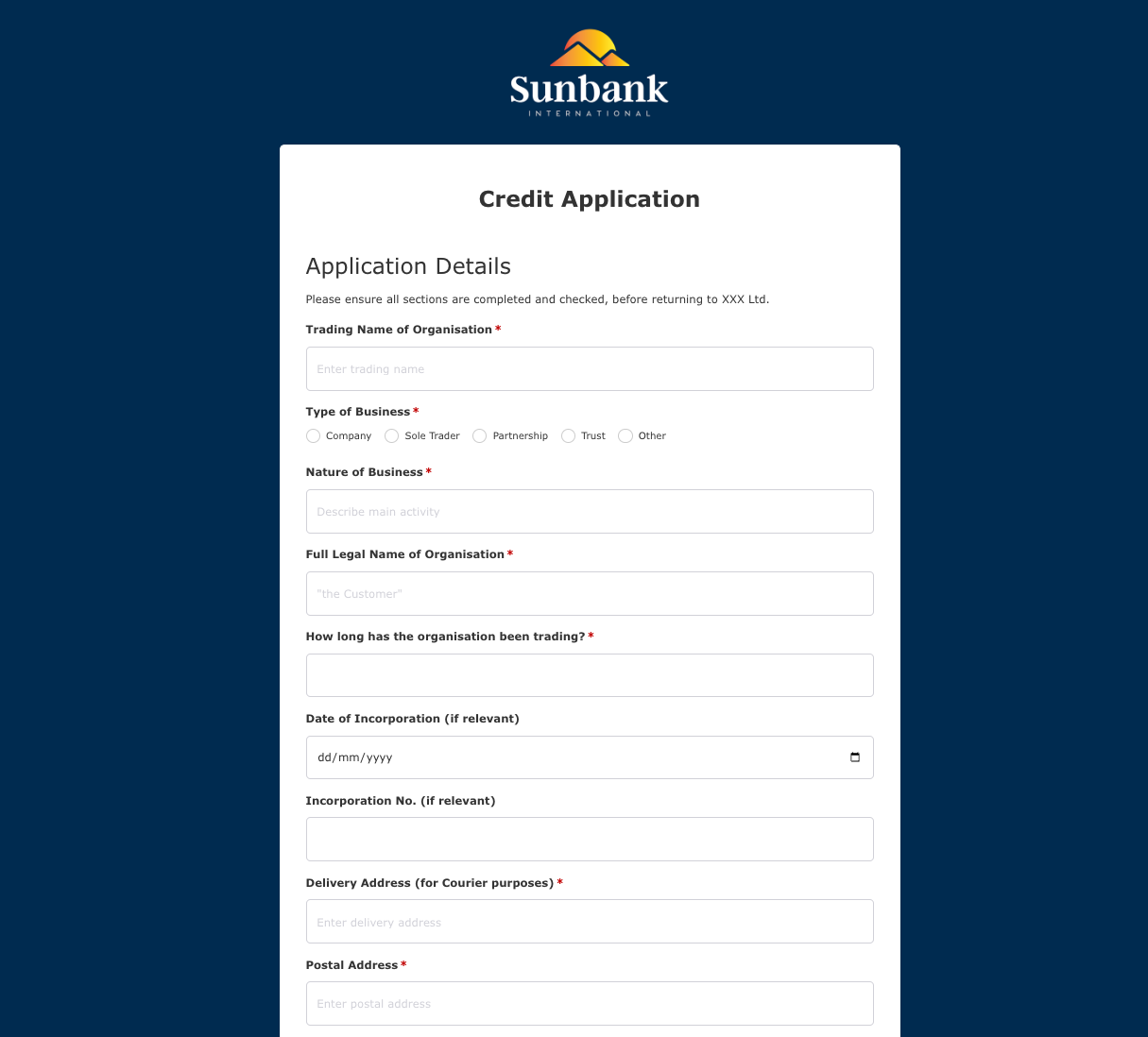 Credit Application Form
Credit Application Form
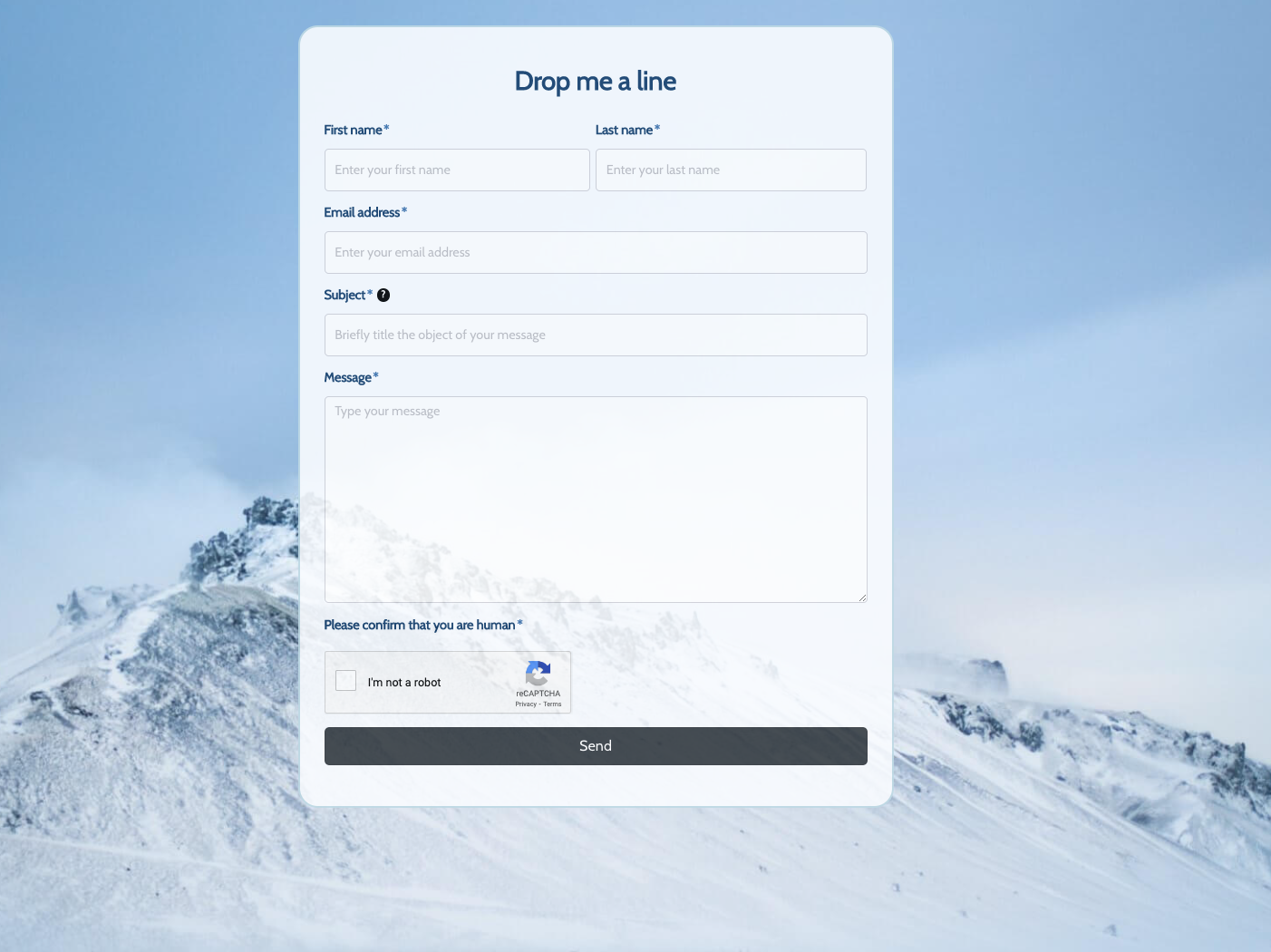 Drop me a line Form
Drop me a line Form
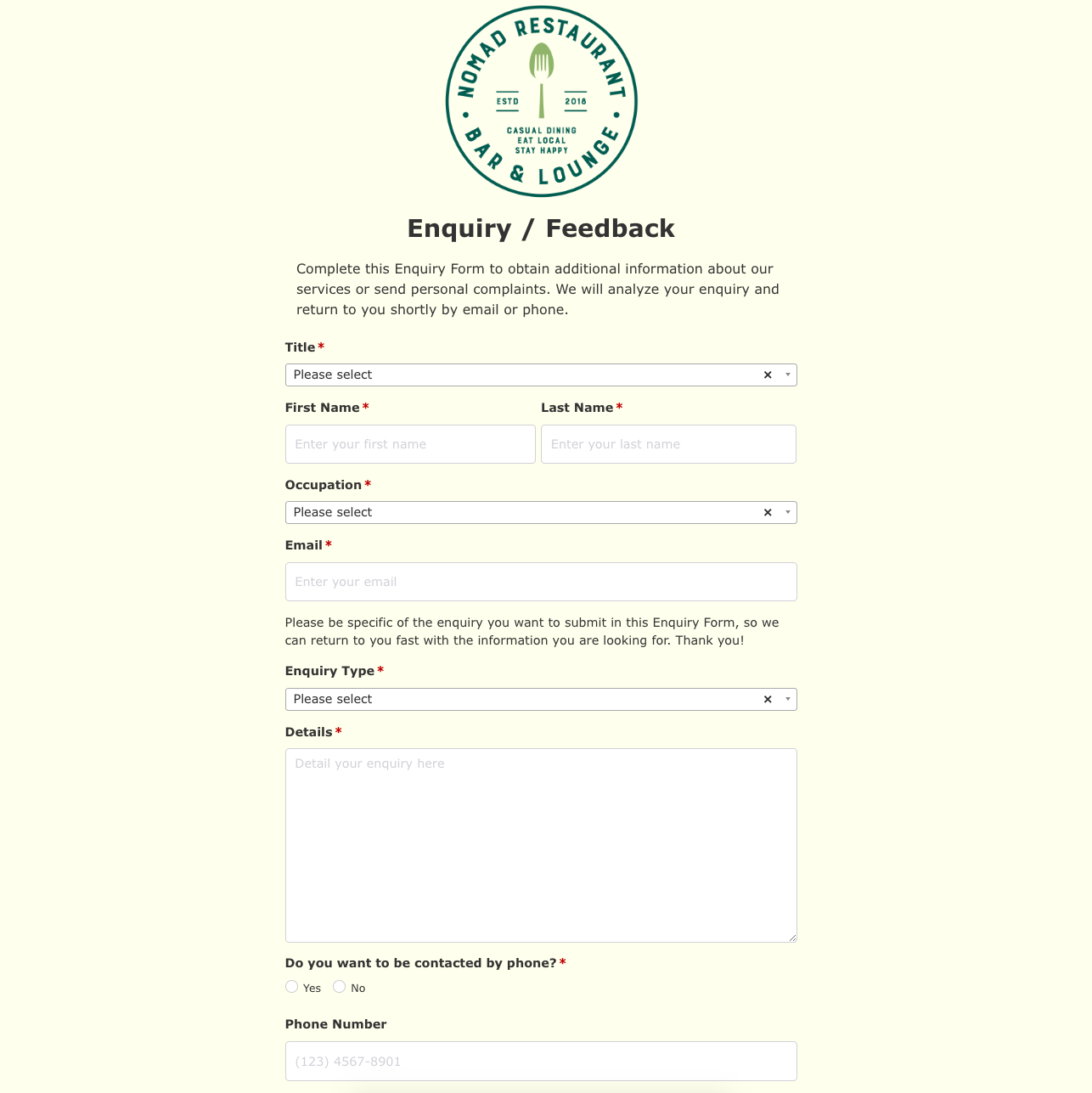 Enquiry / Feedback Form
Enquiry / Feedback Form
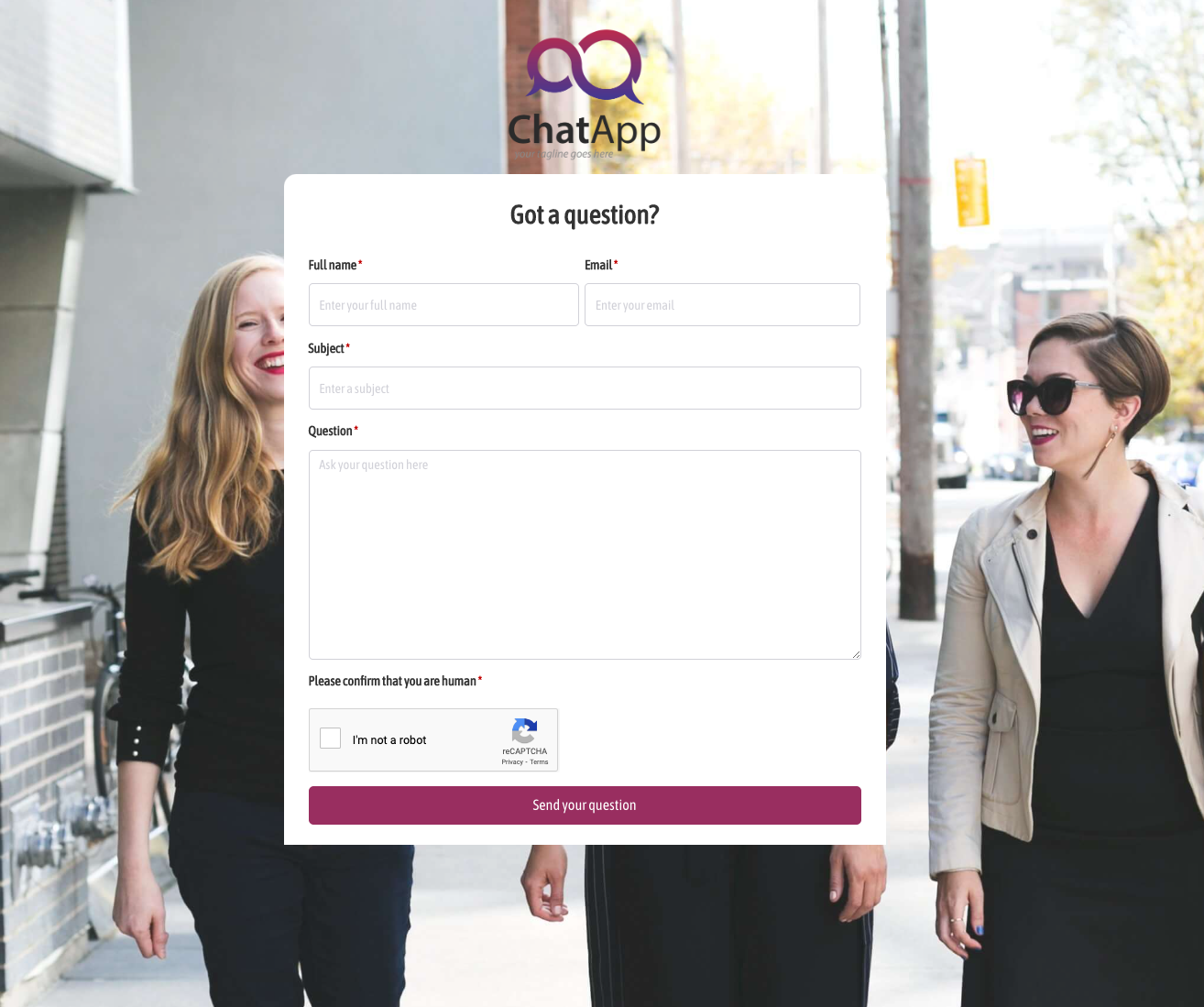 Got a question? Form
Got a question? Form
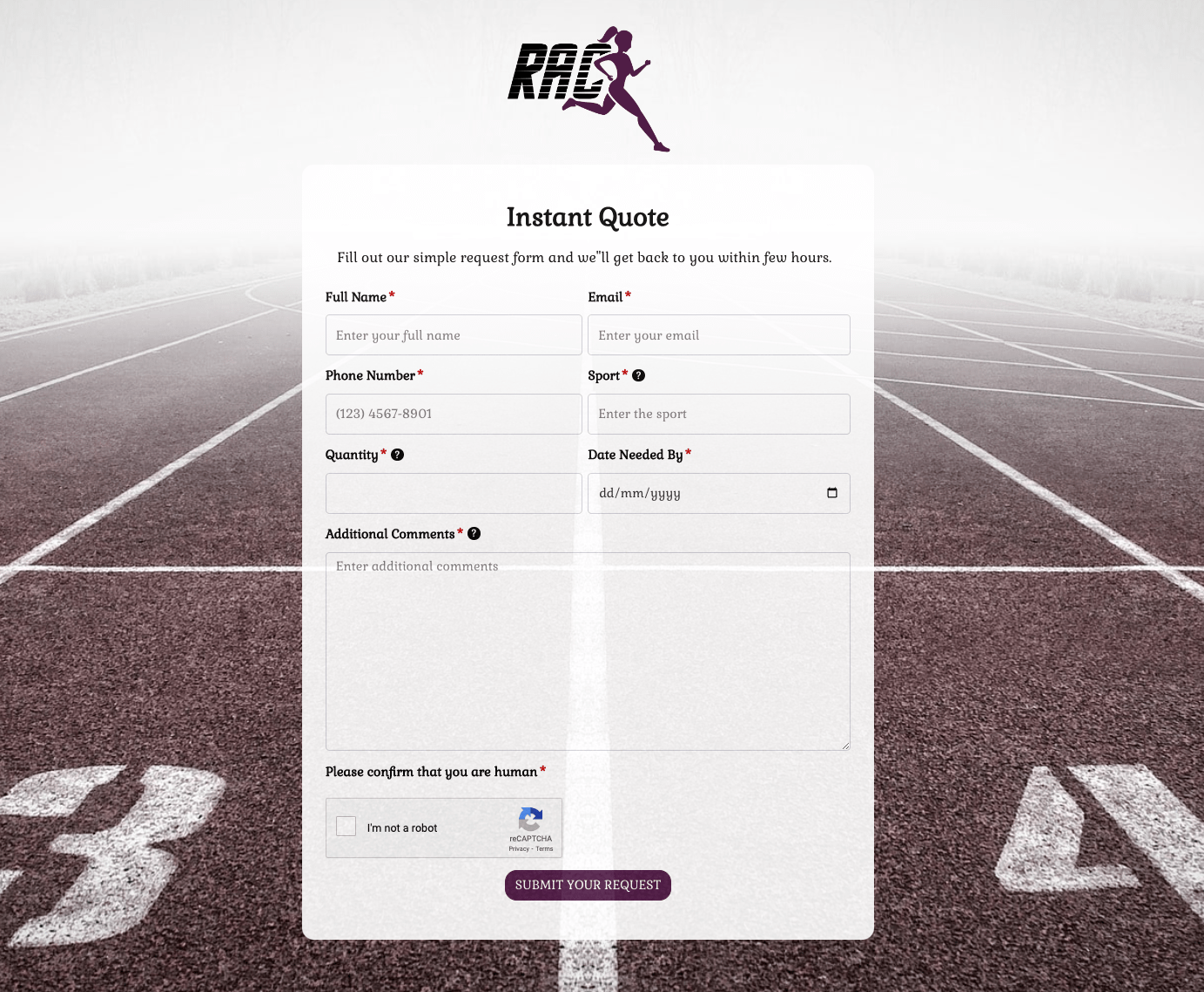 Instant Quote Form
Instant Quote Form
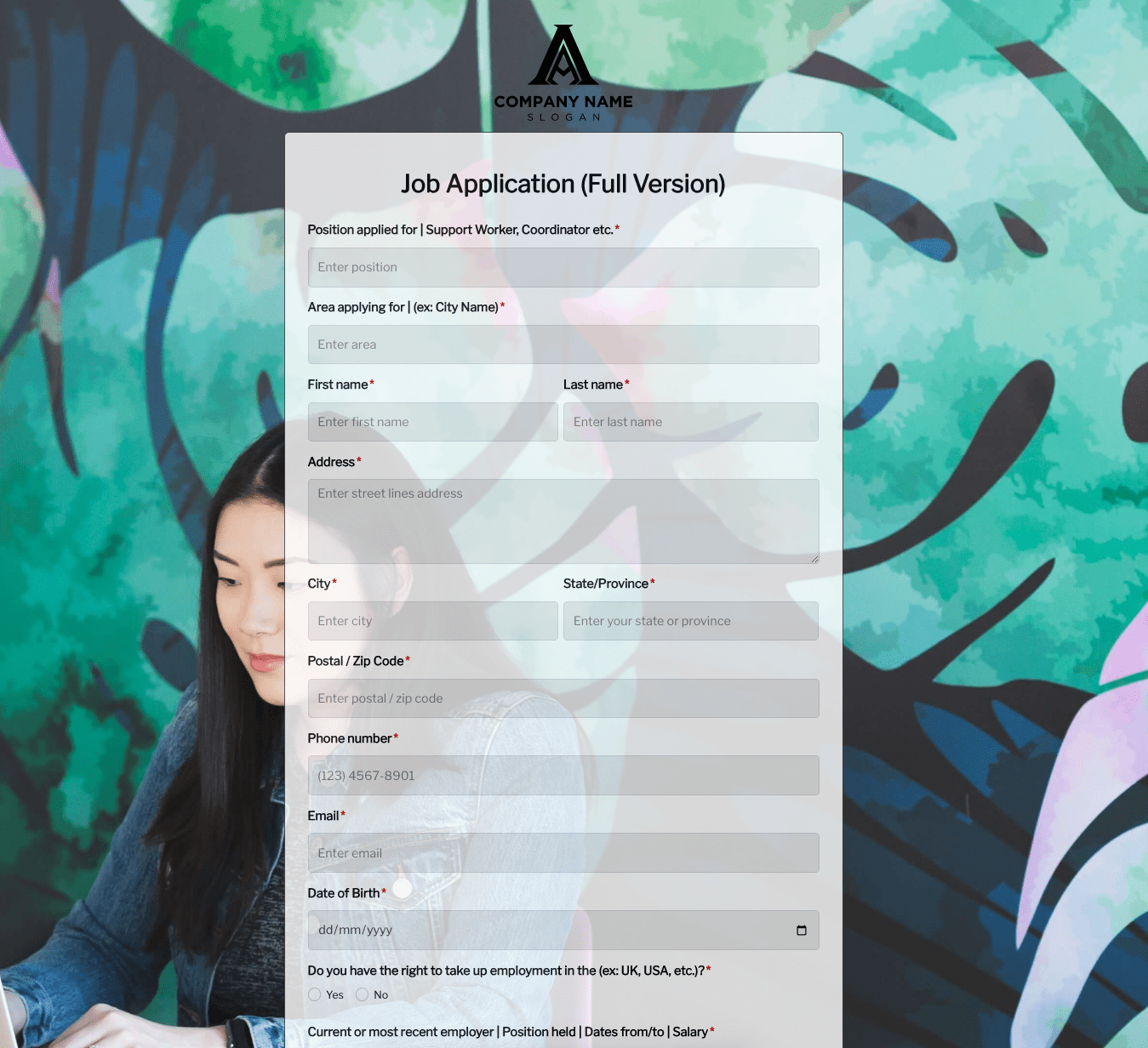 Job Application Form
Job Application Form
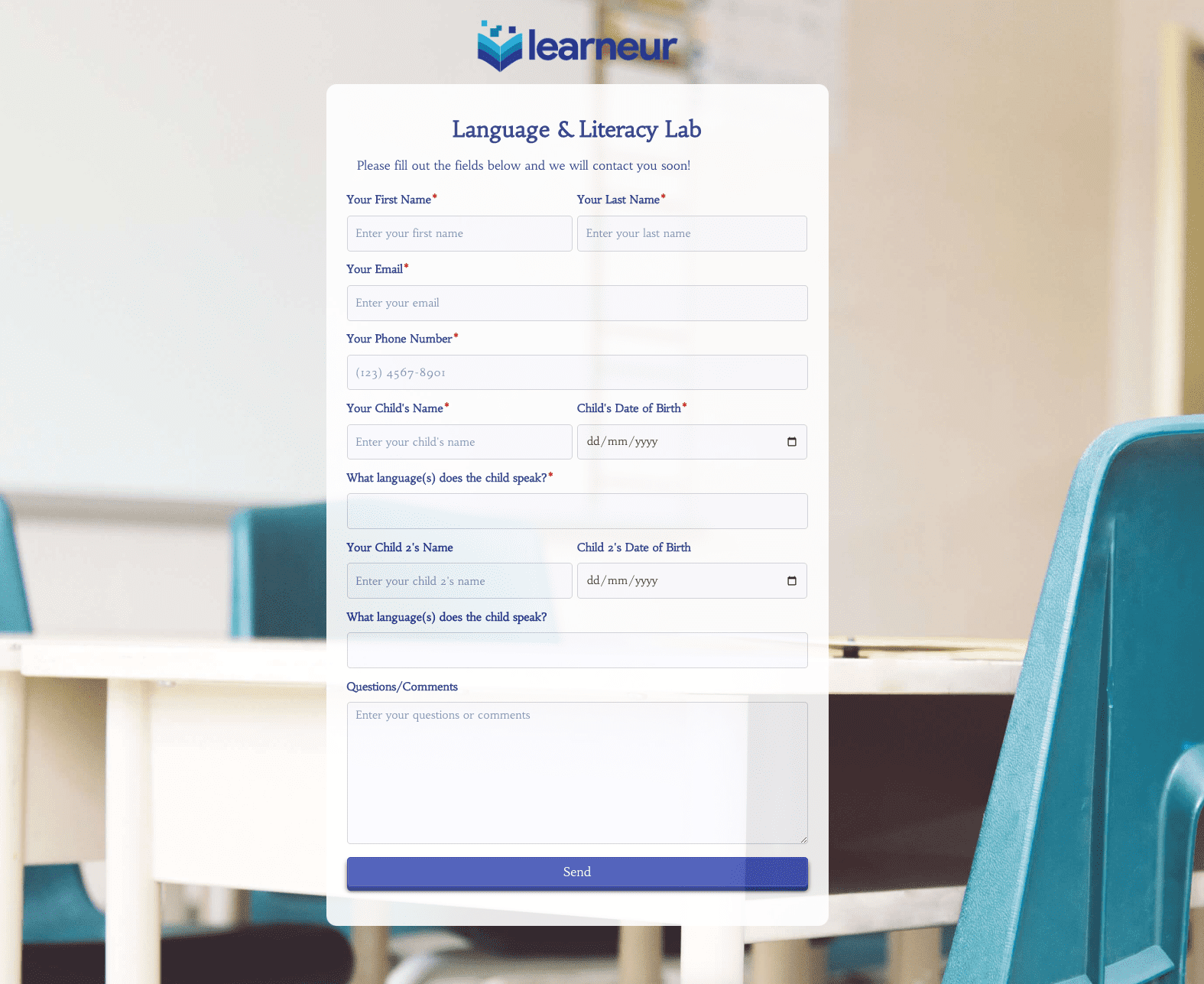 Language & Literacy Lab Form
Language & Literacy Lab Form
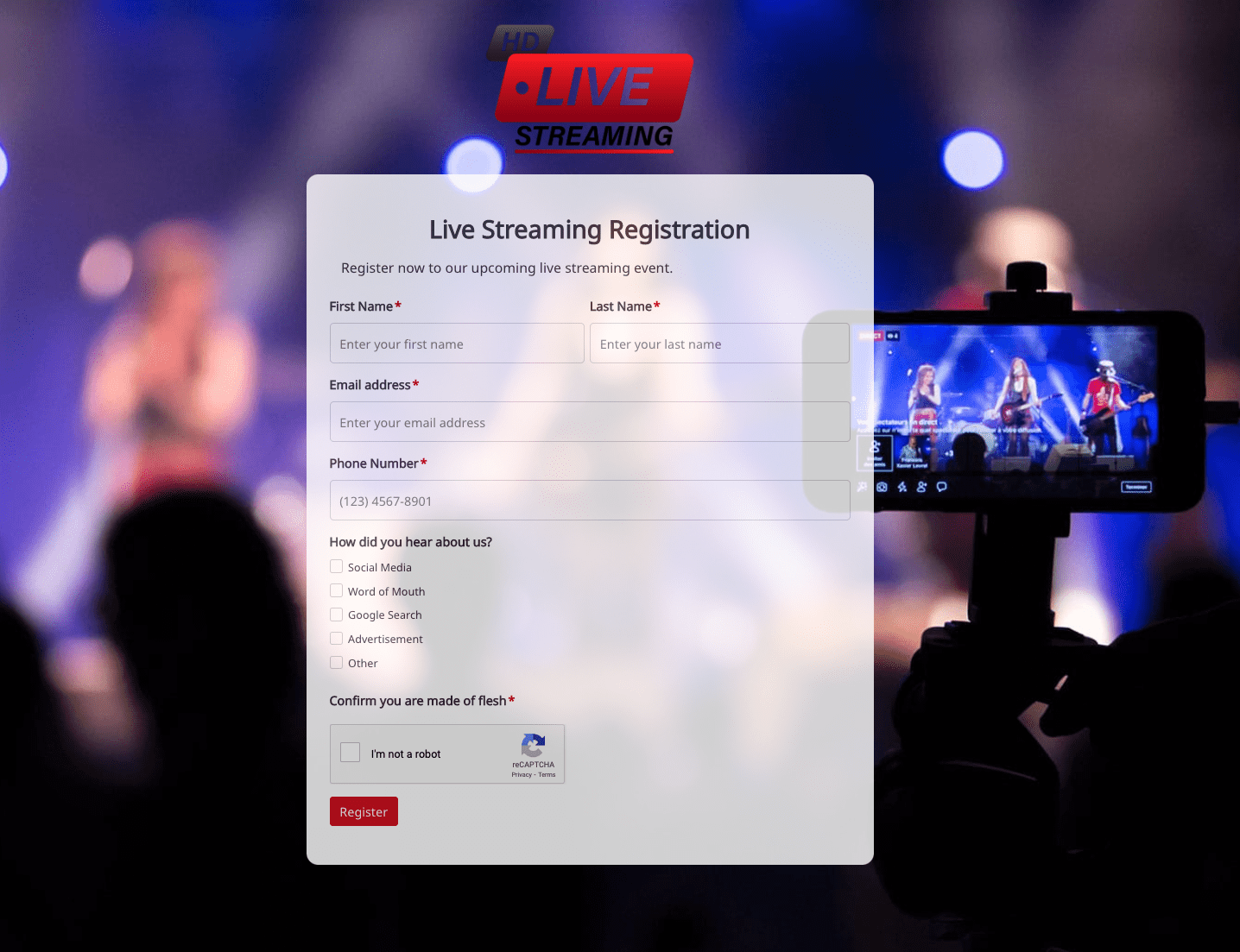 Live Streaming Registration Form
Live Streaming Registration Form
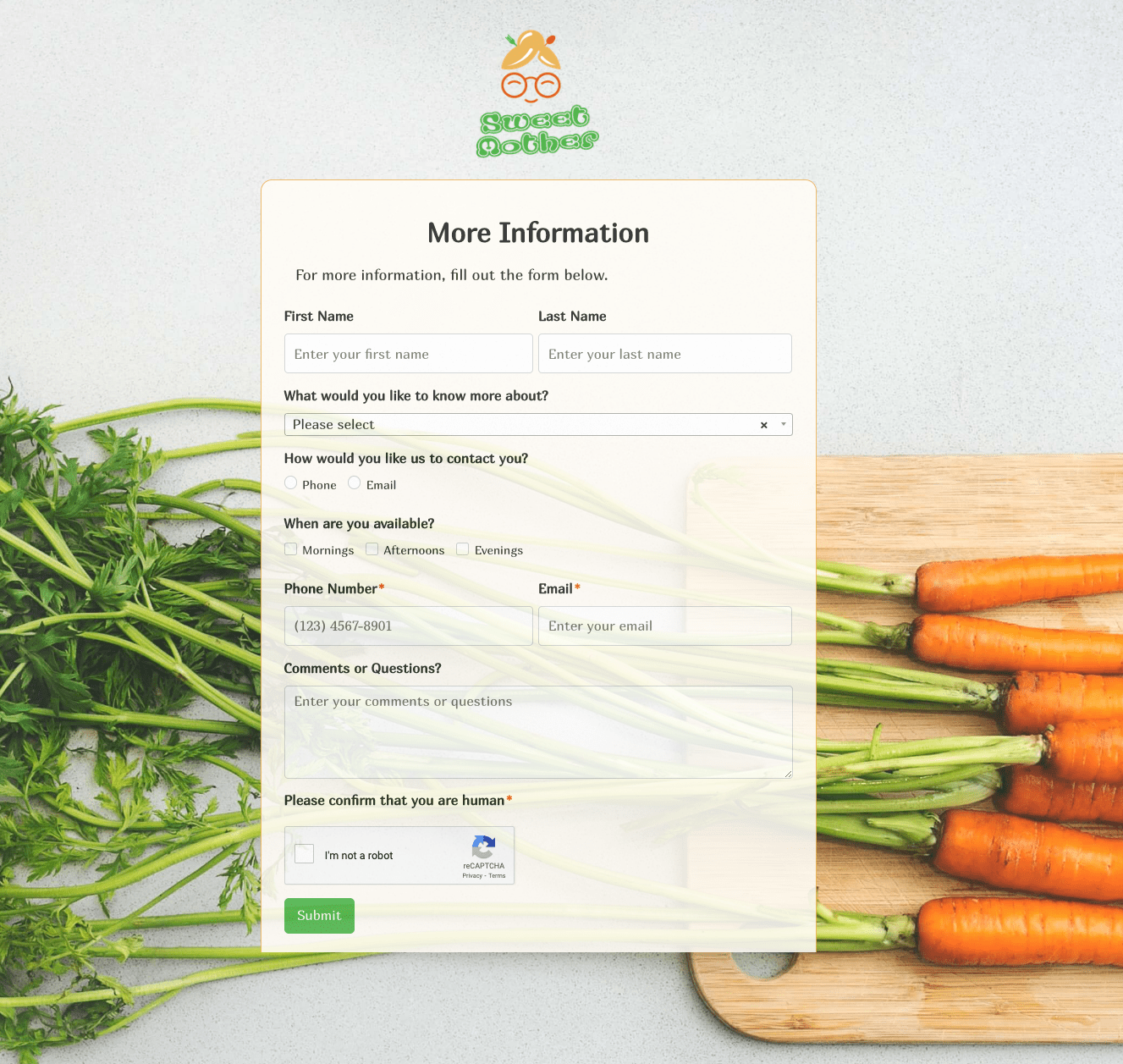 More Information Form
More Information Form
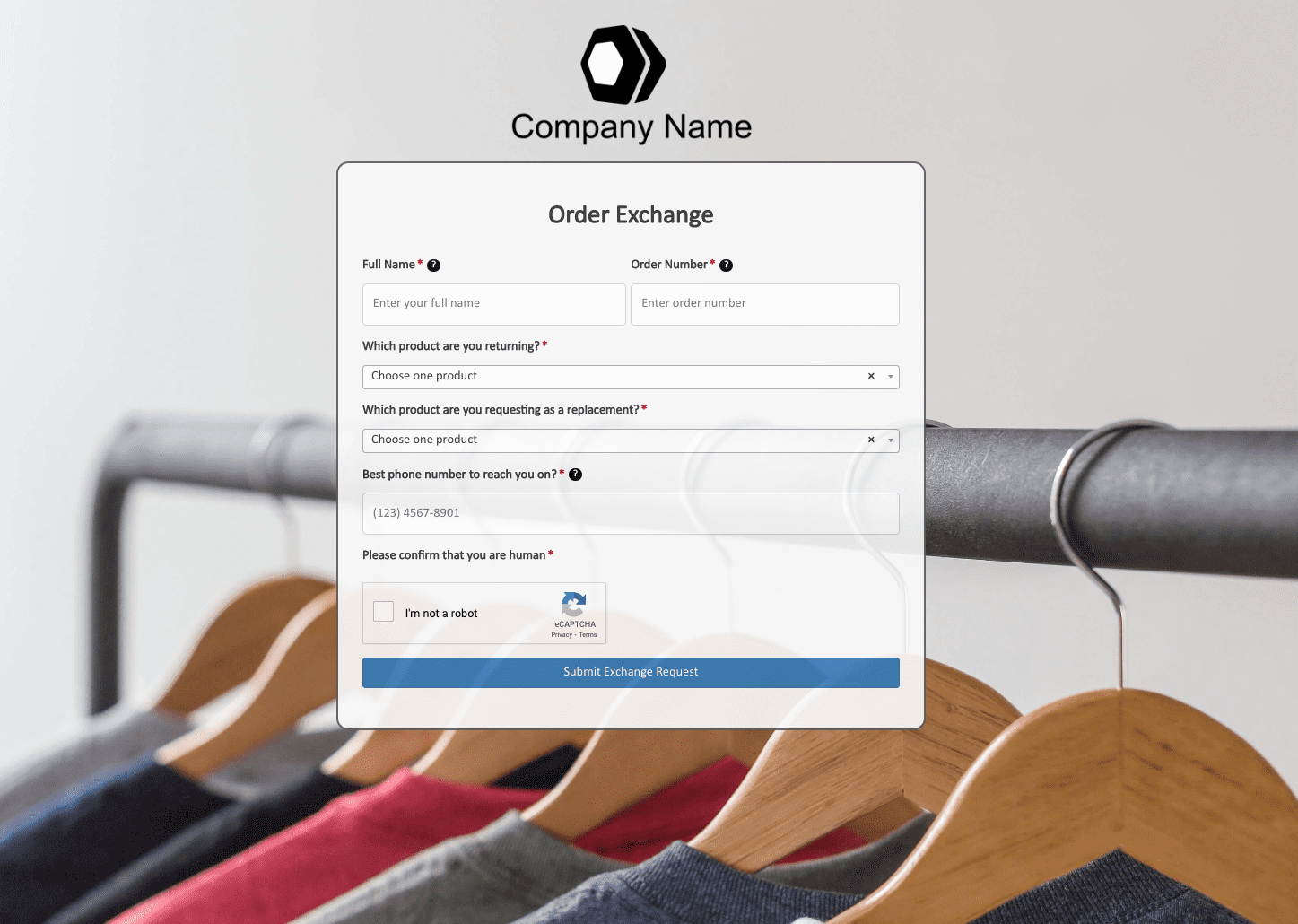 Order Exchange Form
Order Exchange Form
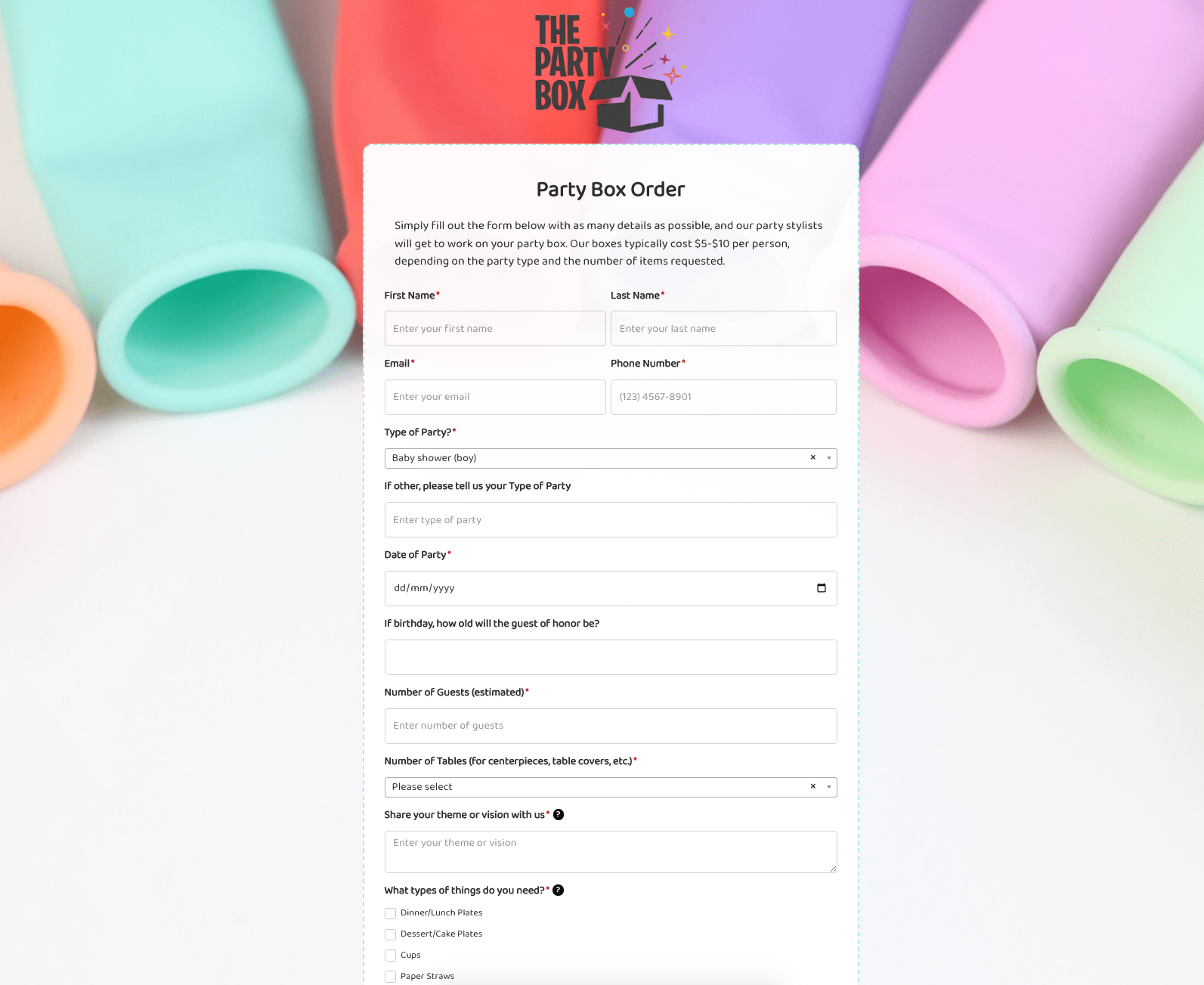 Party Box Order Form
Party Box Order Form
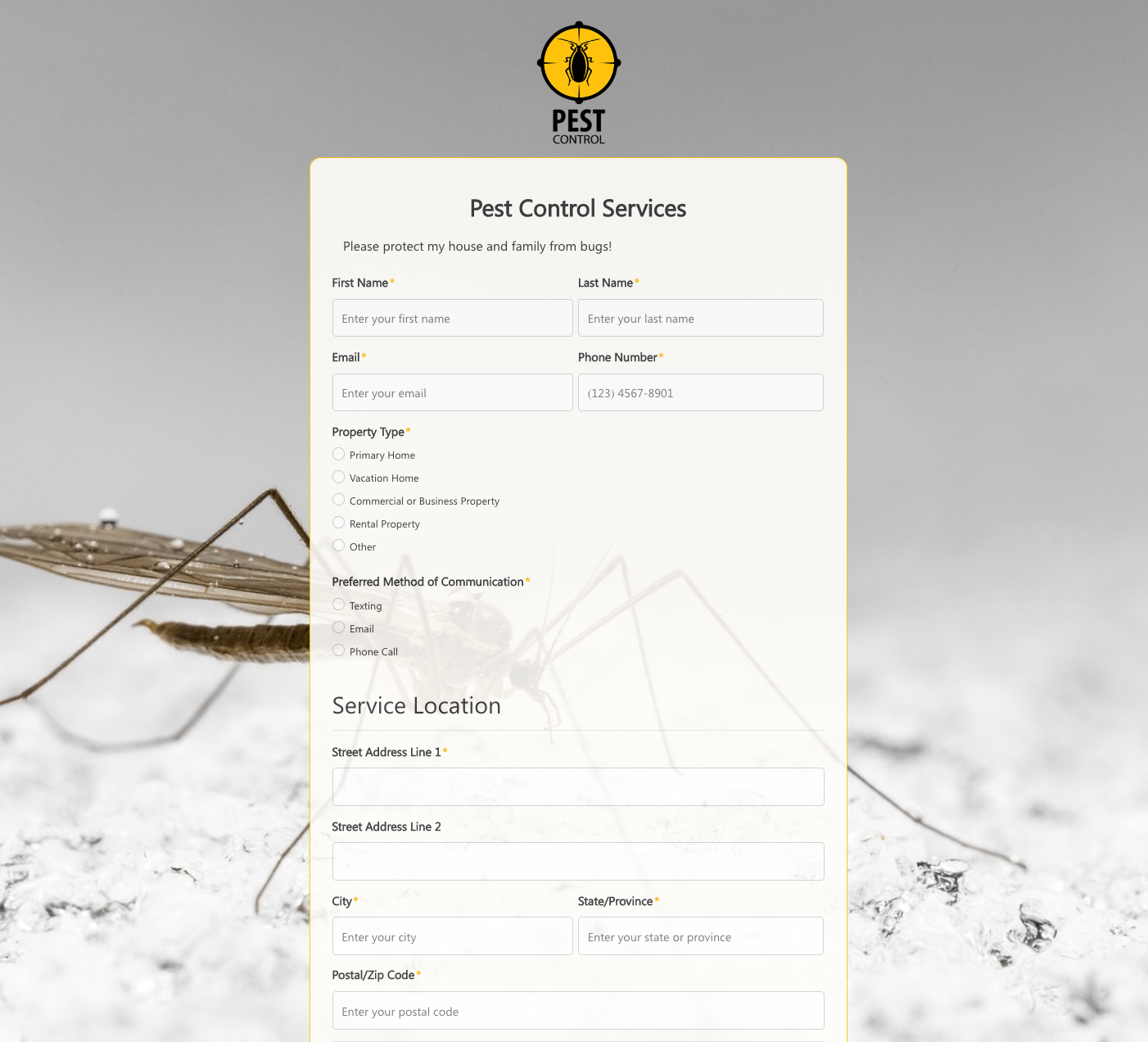 Pest Control Services Form
Pest Control Services Form
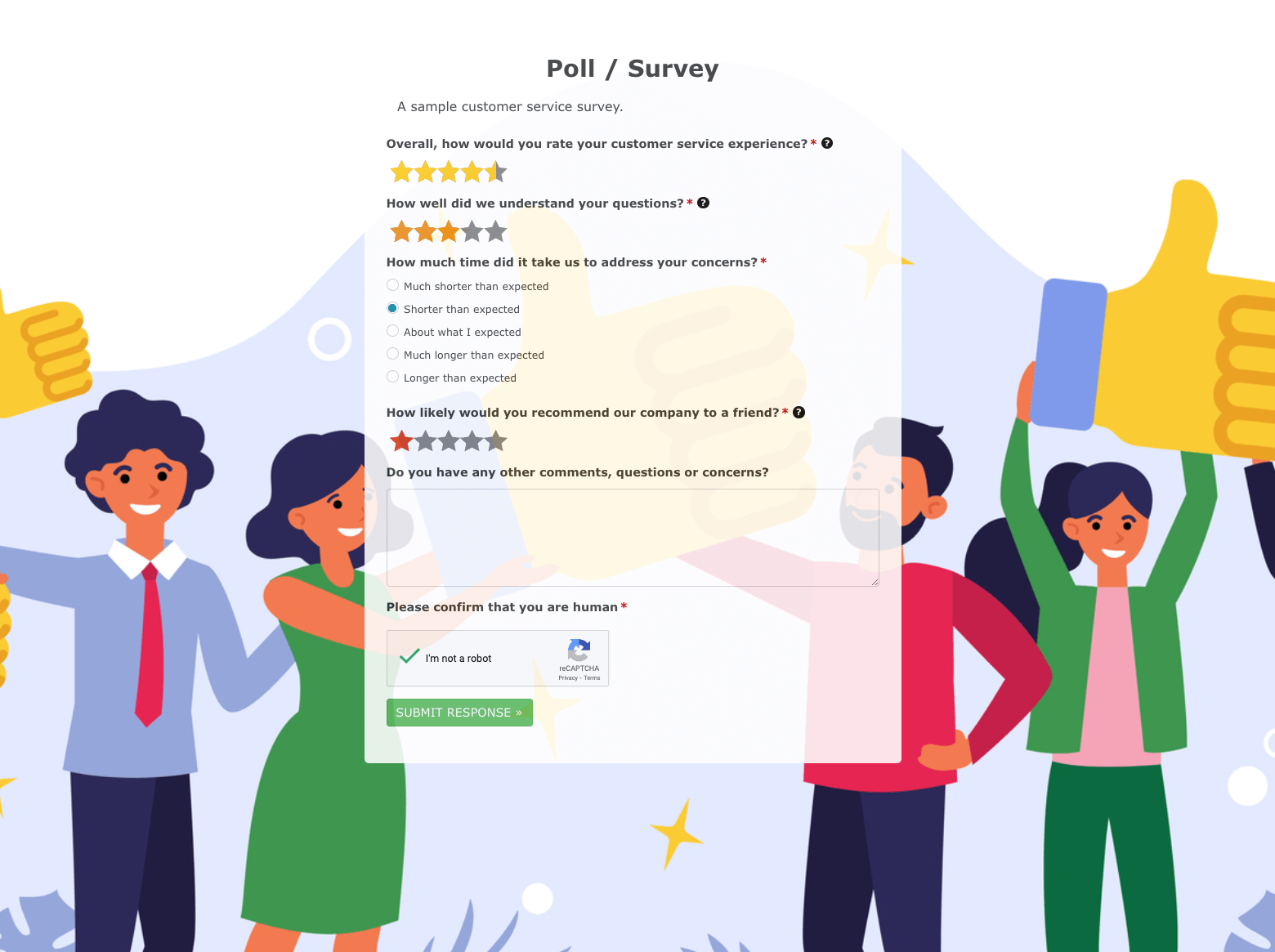 Poll / Survey Form
Poll / Survey Form
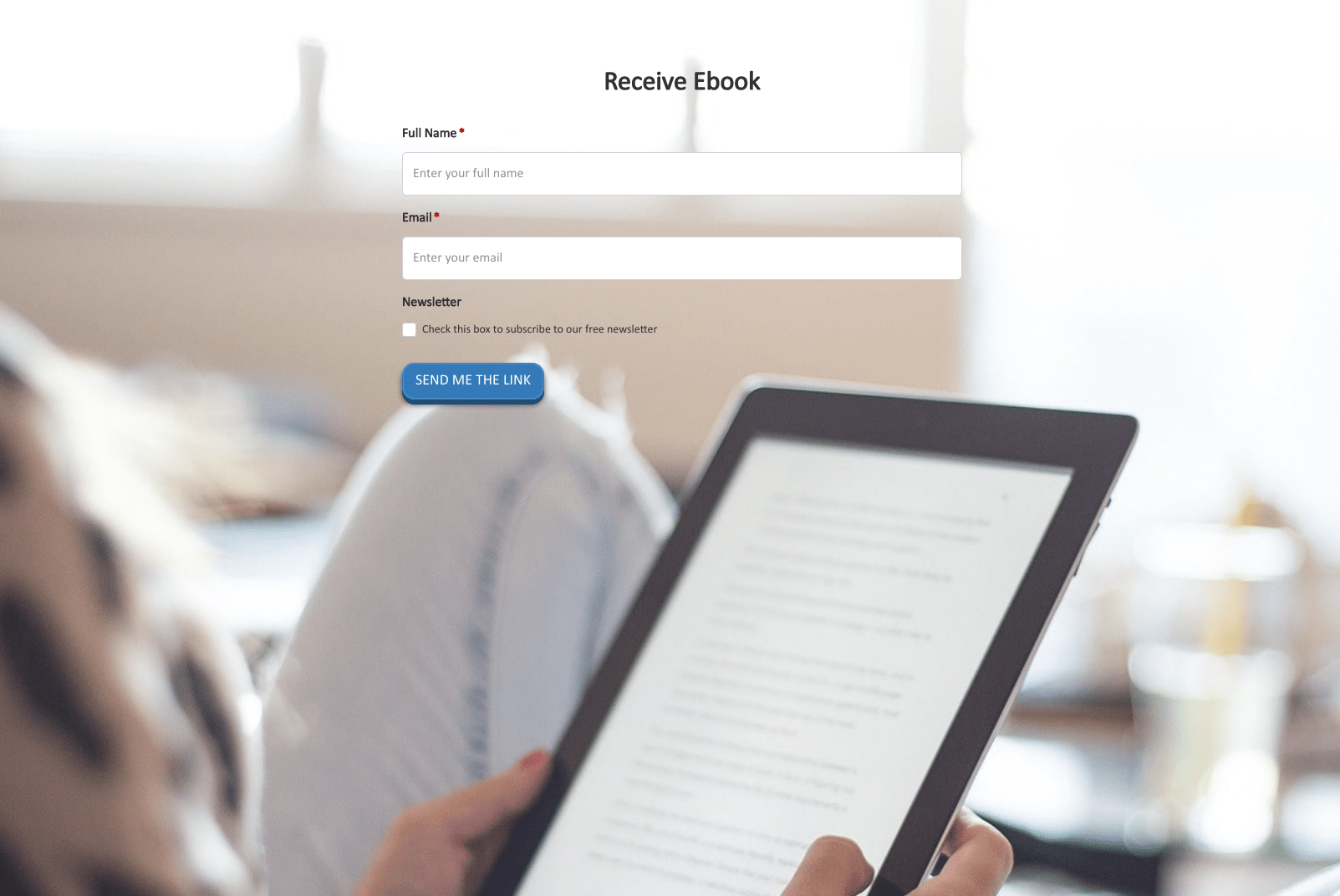 Receive Ebook Form
Receive Ebook Form
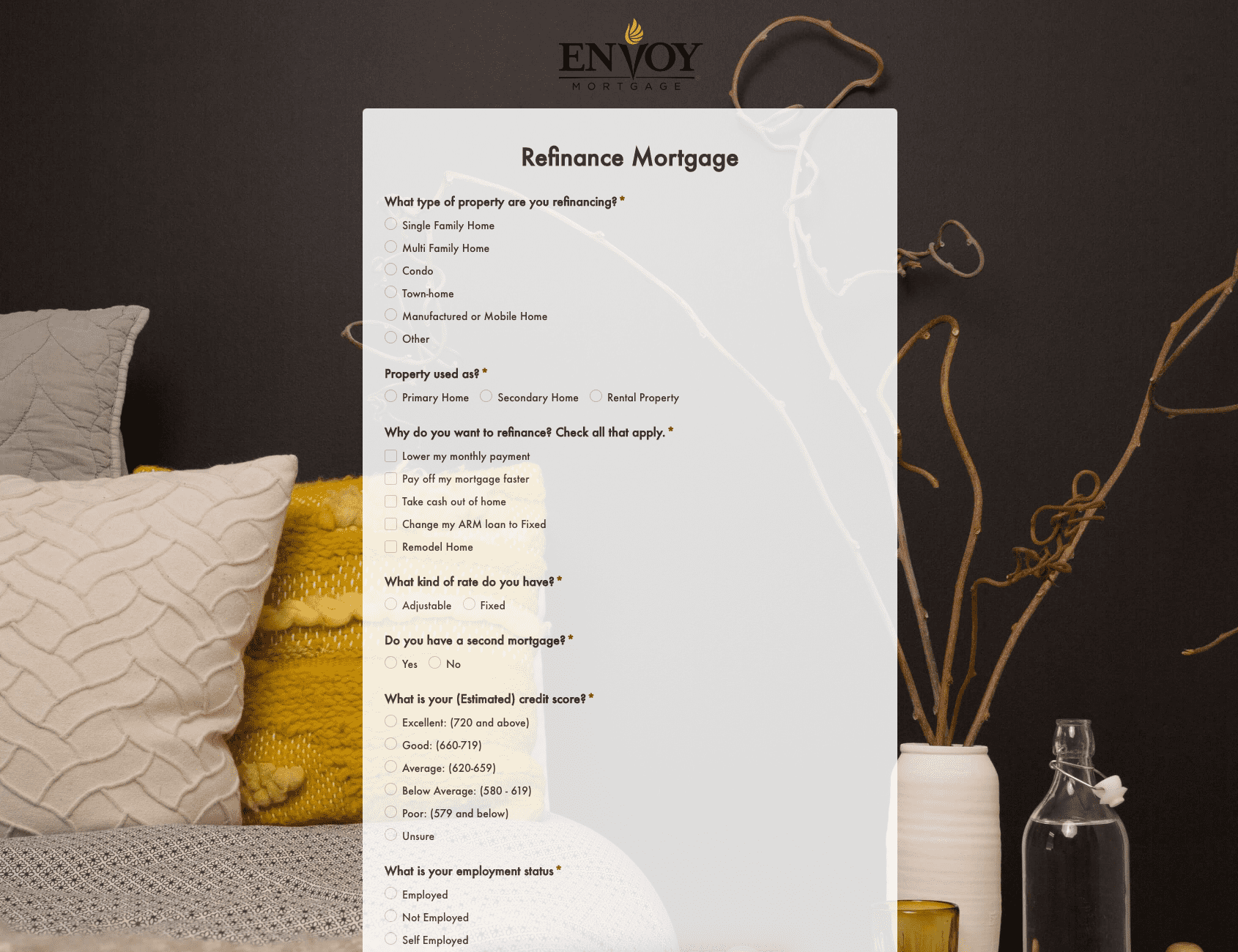 Refinance Mortgage Form
Refinance Mortgage Form
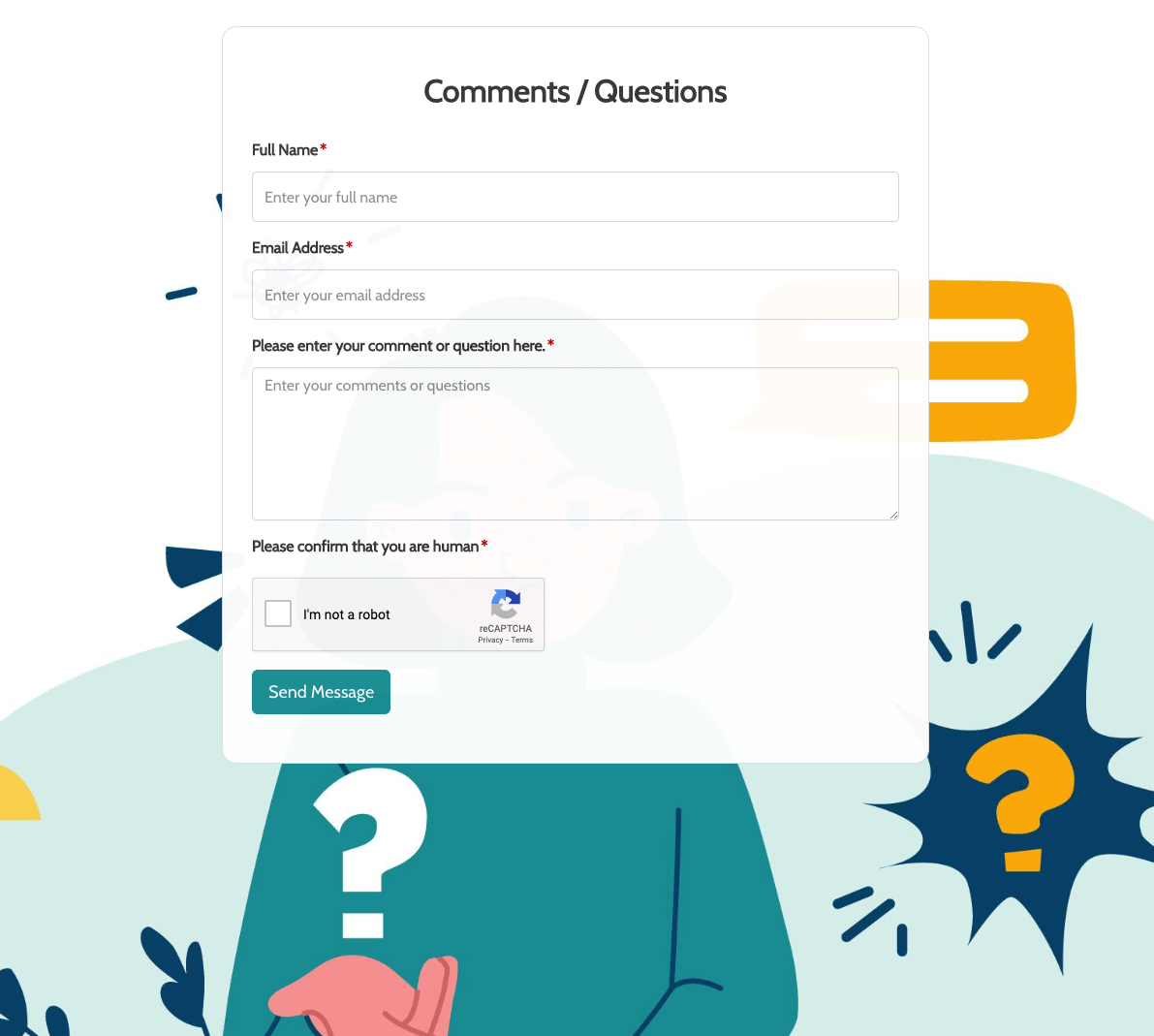 Remarks / Questions Form
Remarks / Questions Form
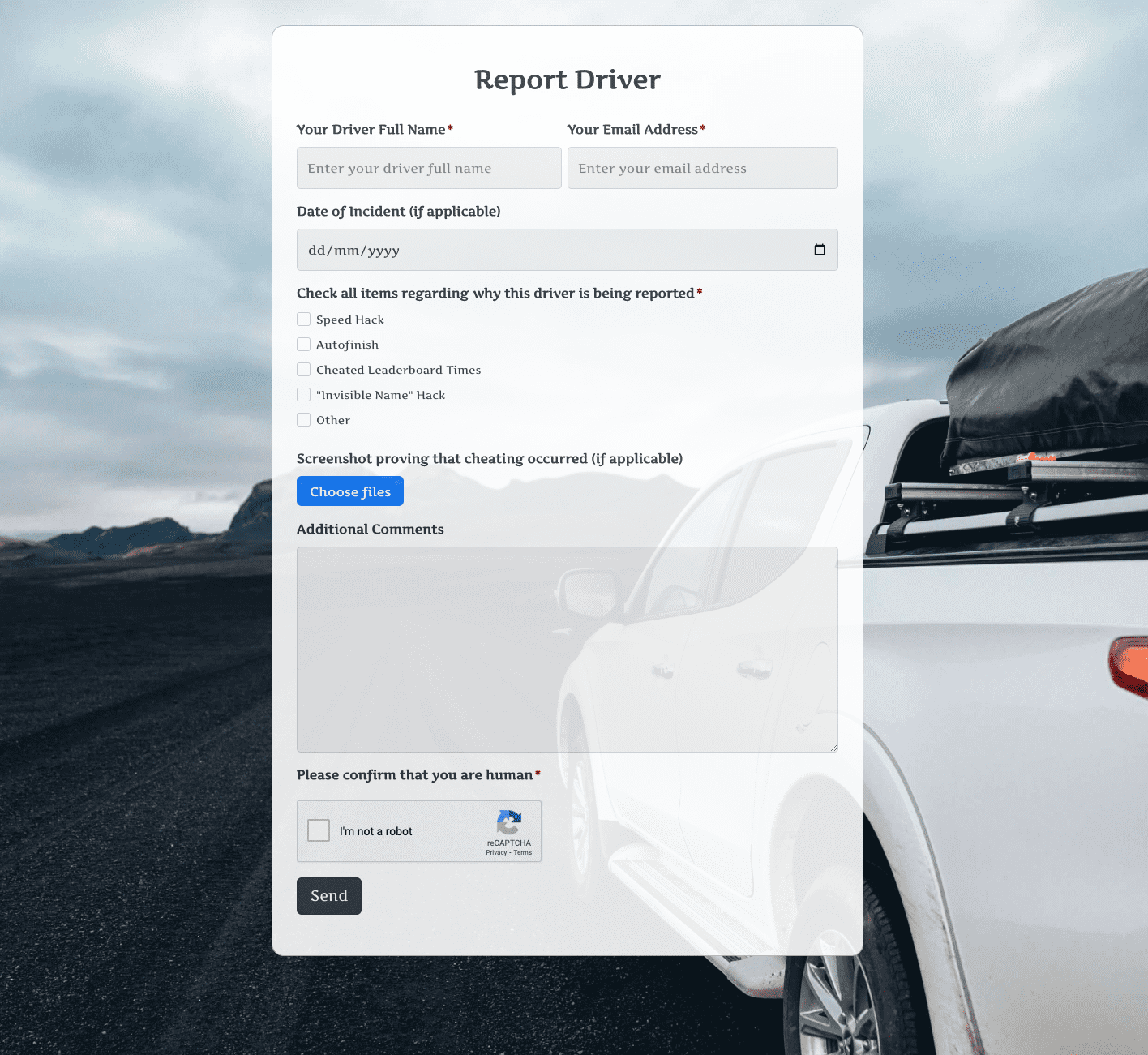 Report Driver Form
Report Driver Form
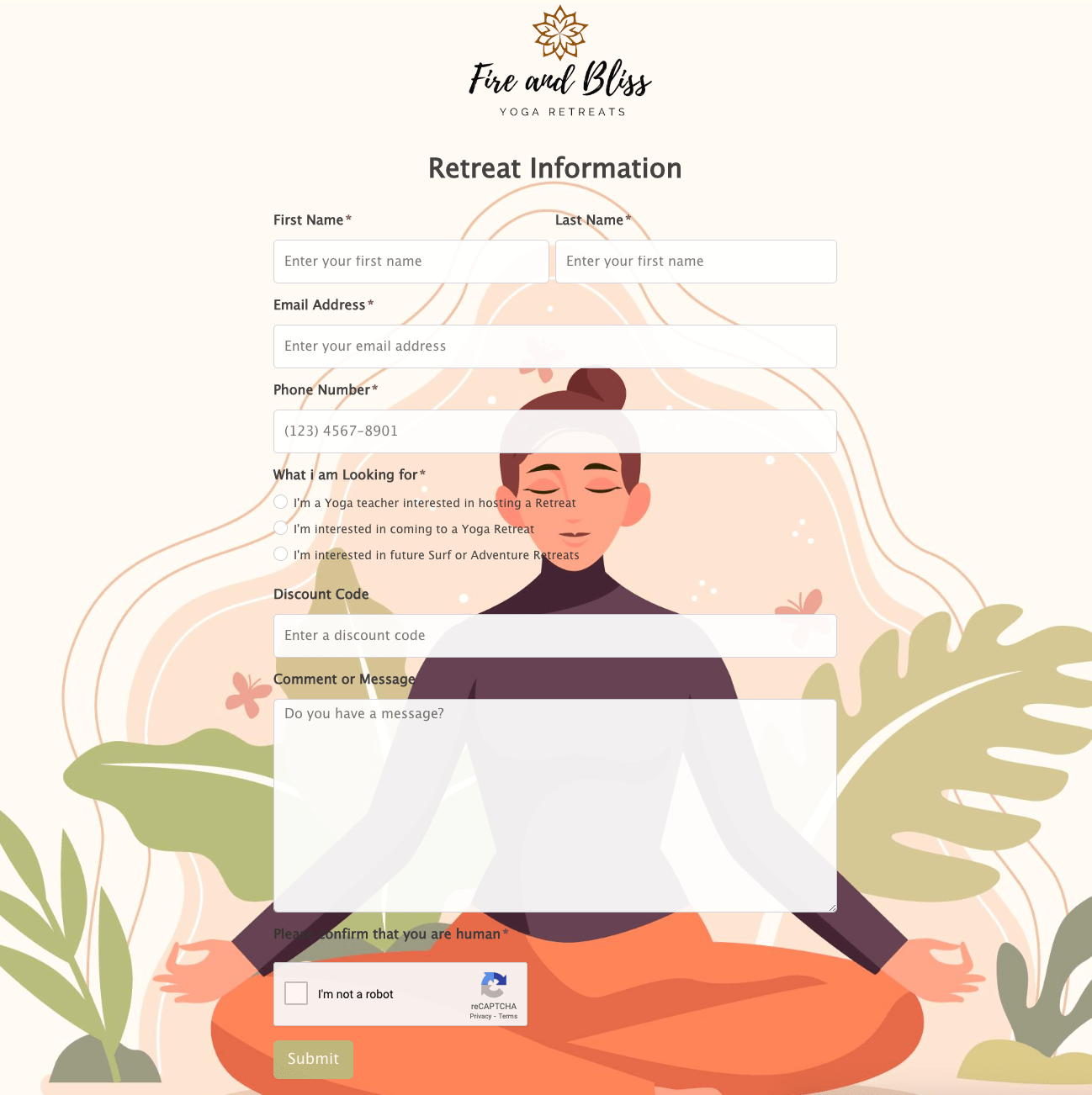 Retreat Information Form
Retreat Information Form
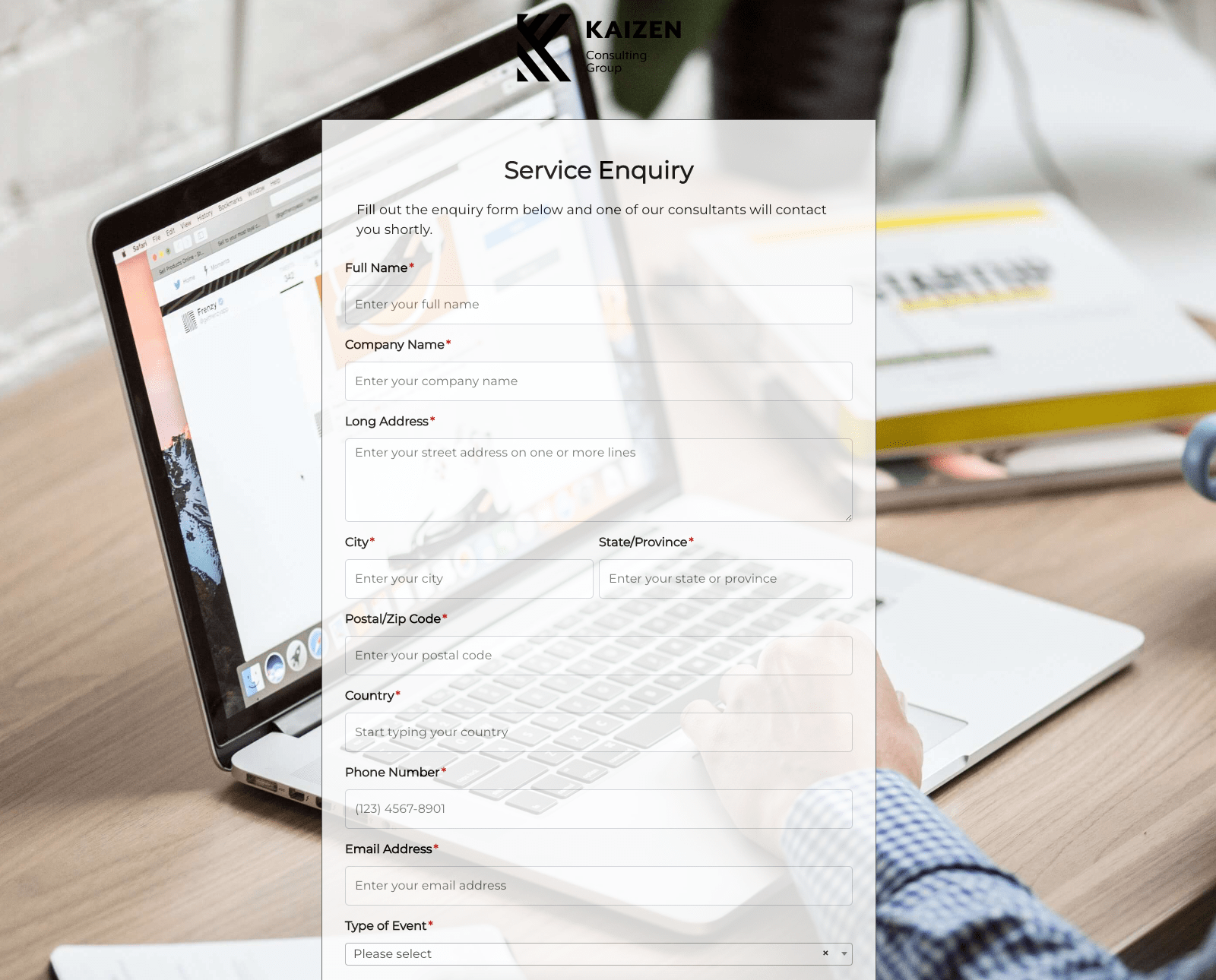 Service Enquiry Form
Service Enquiry Form
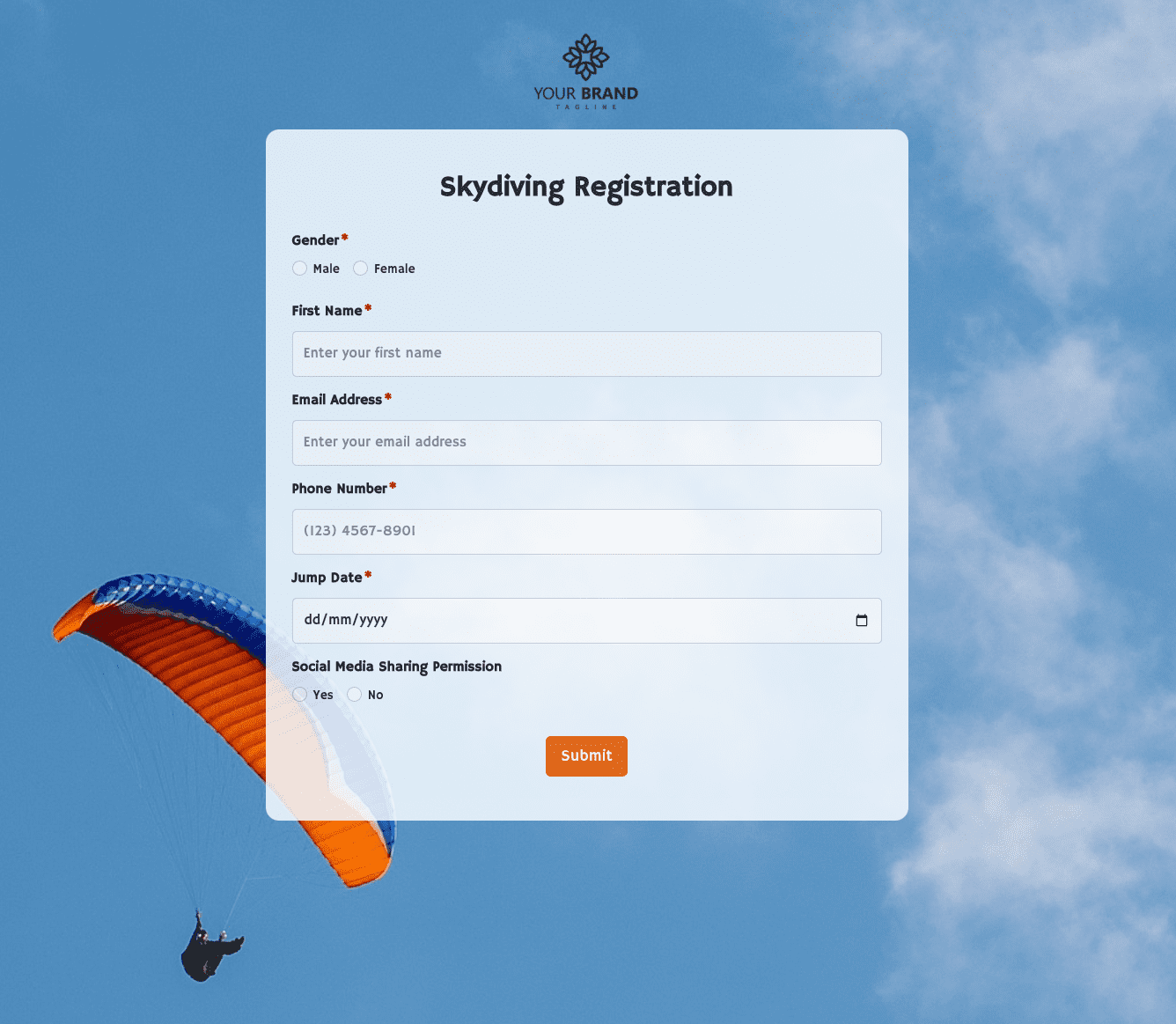 Skydiving Registration Form
Skydiving Registration Form
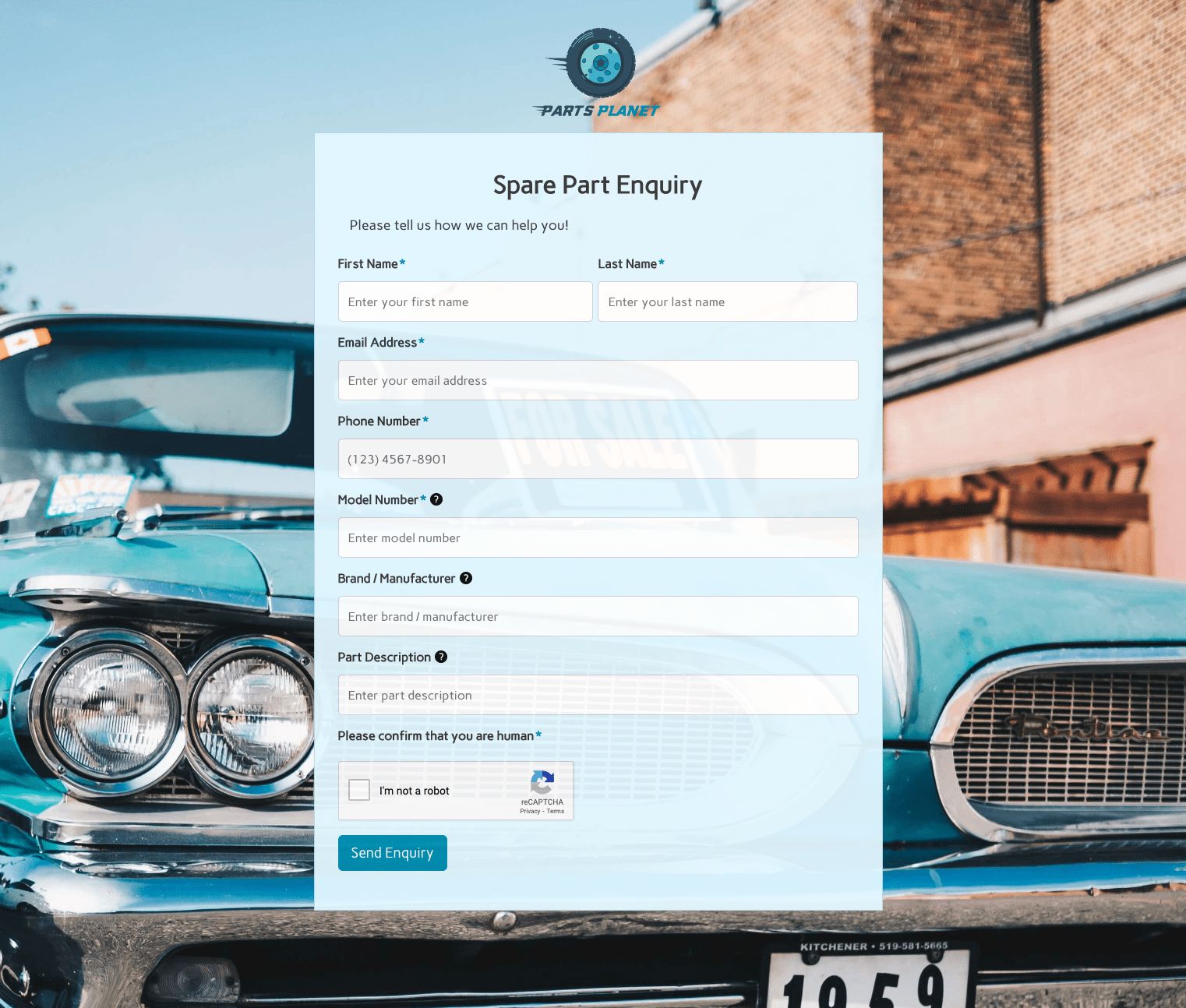 Spare Part Enquiry Form
Spare Part Enquiry Form
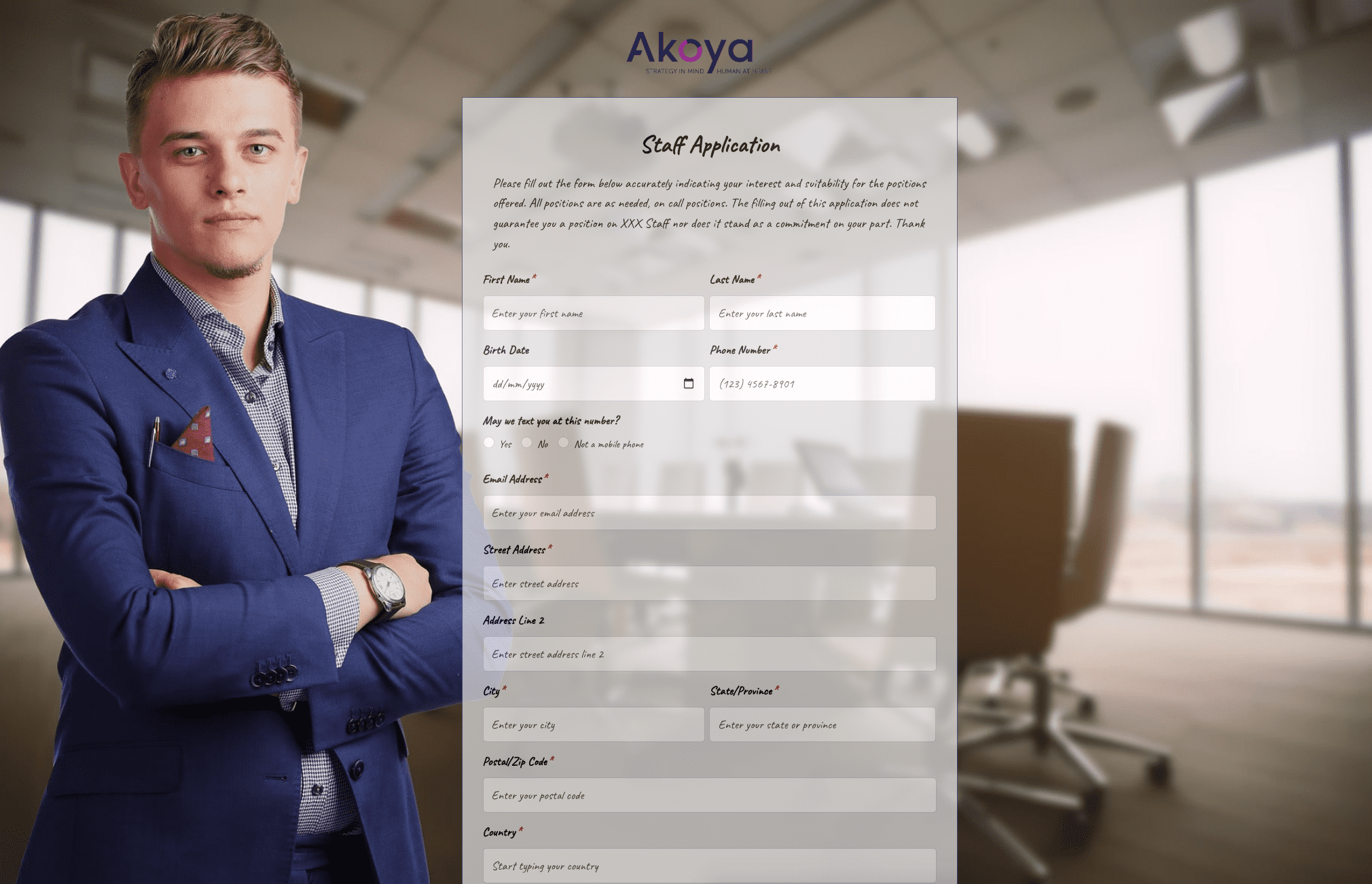 Staff Application Form
Staff Application Form
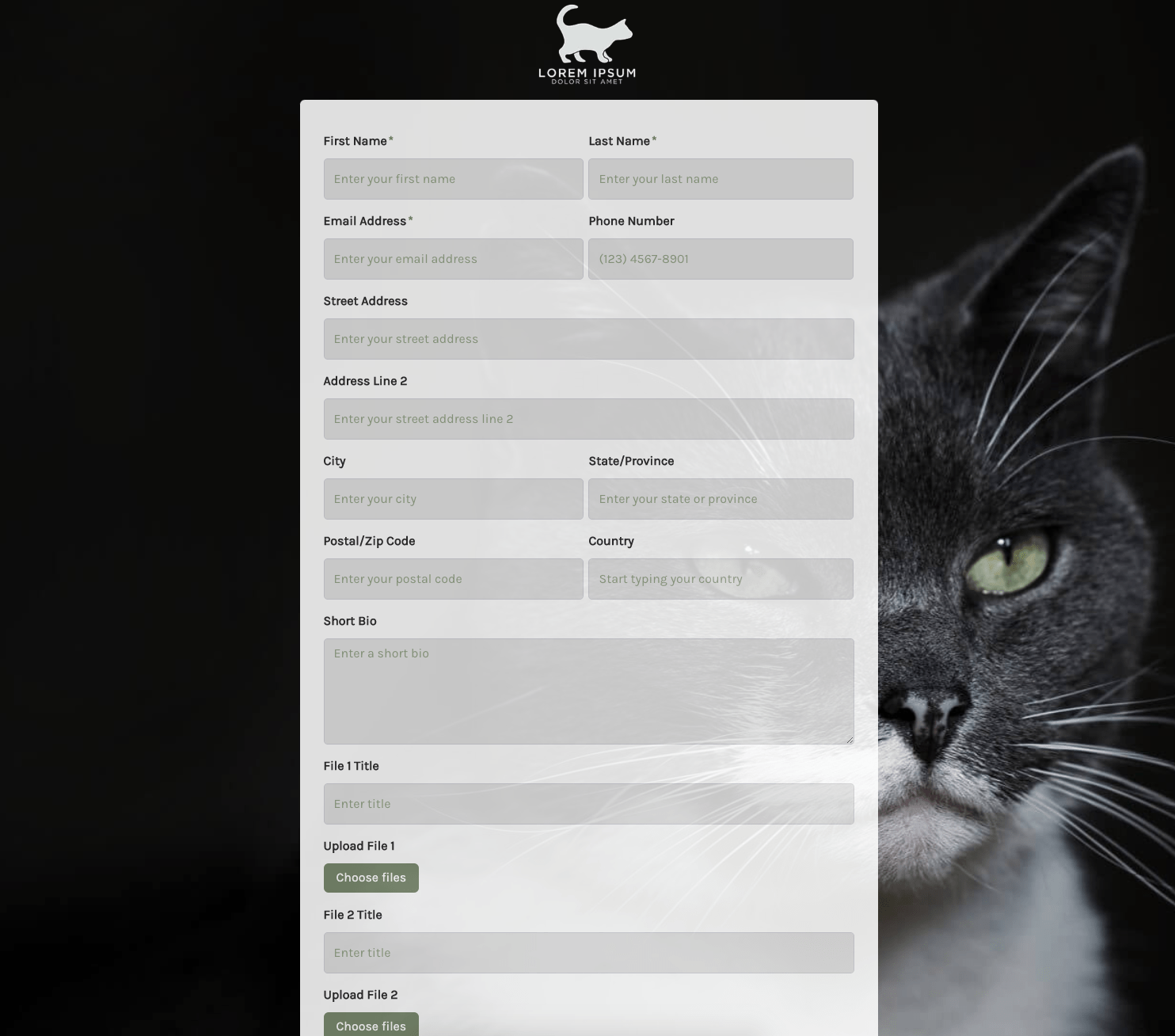 Submission Form
Submission Form
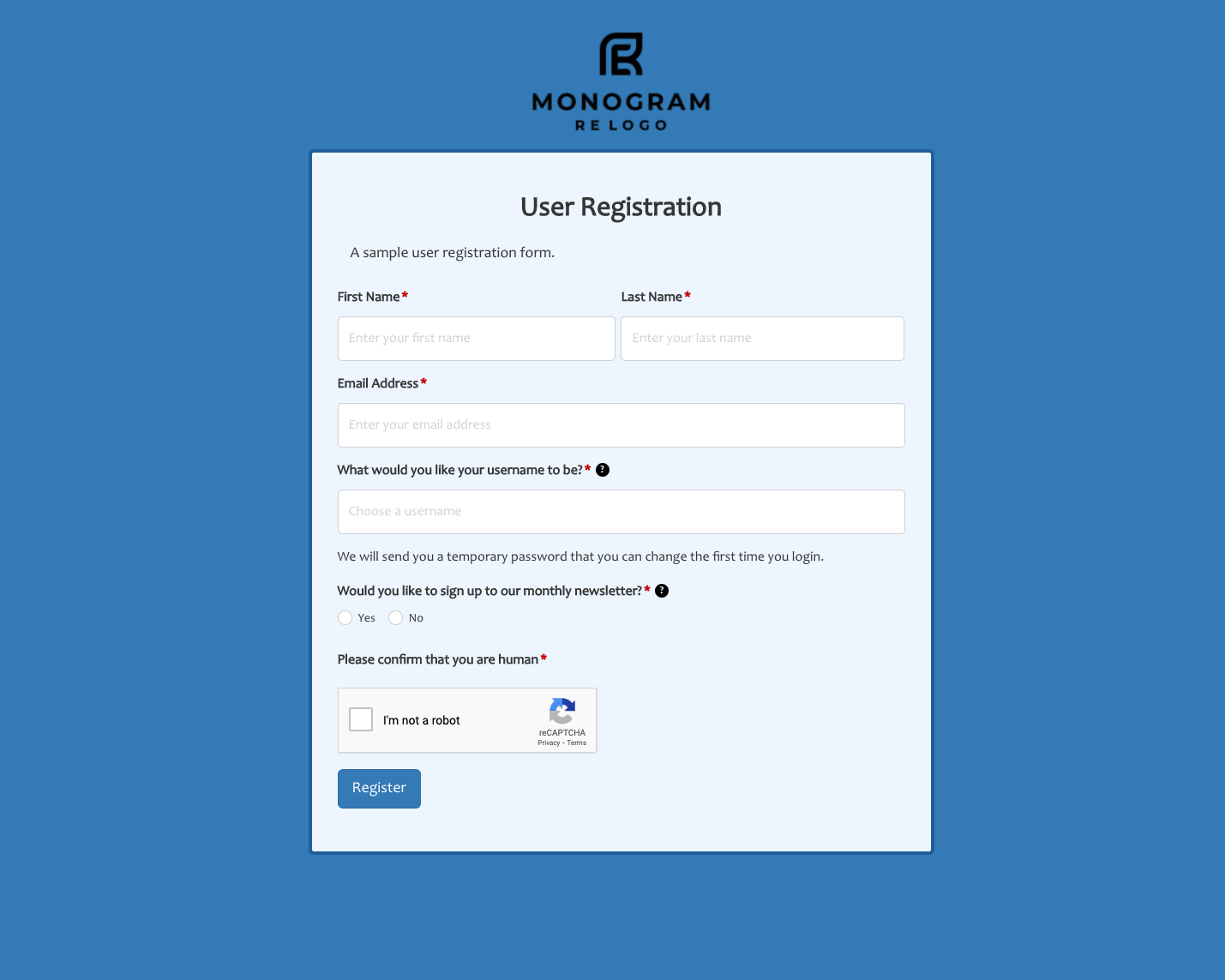 User Registration Form
User Registration Form
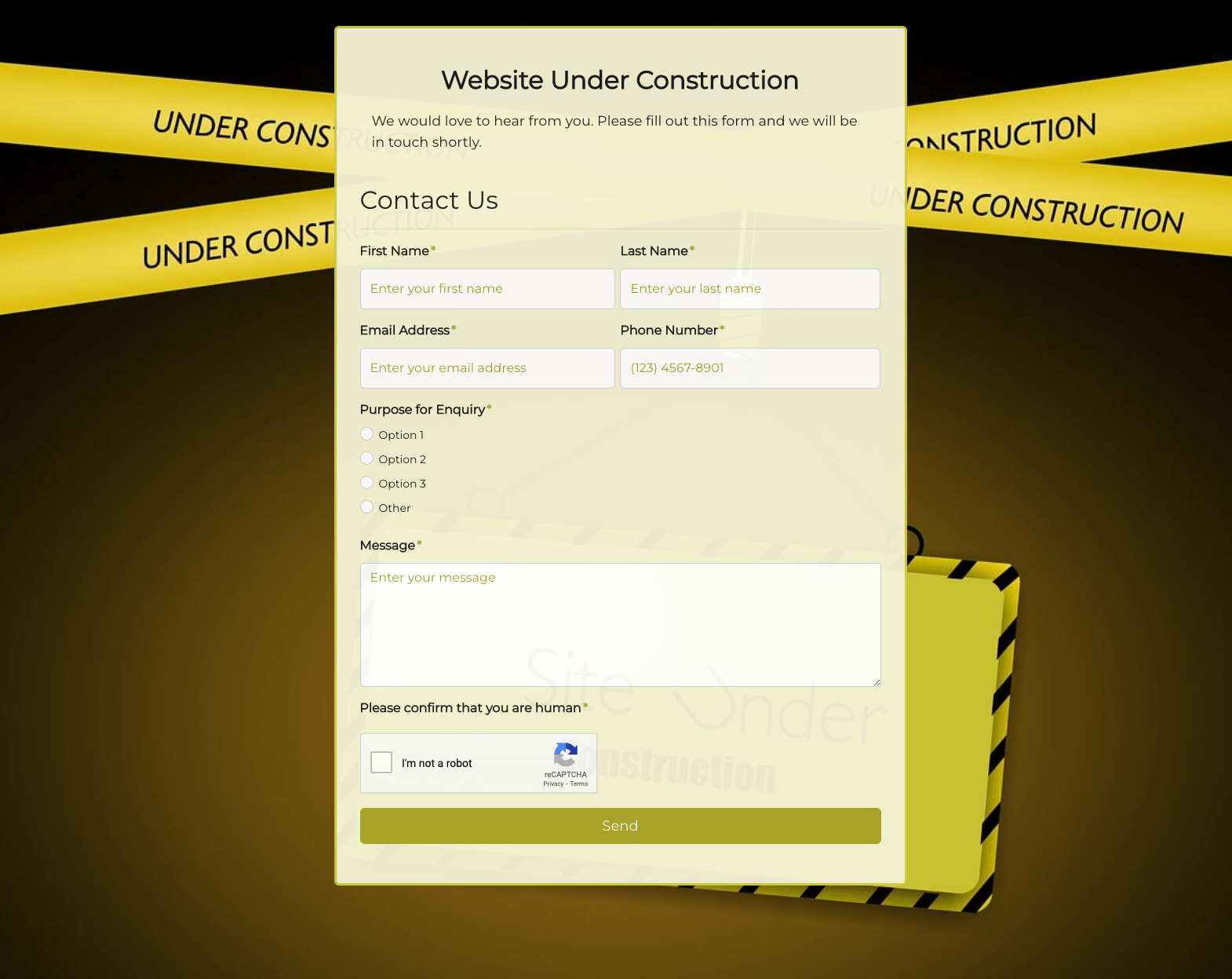 Website Under Construction Form
Website Under Construction Form
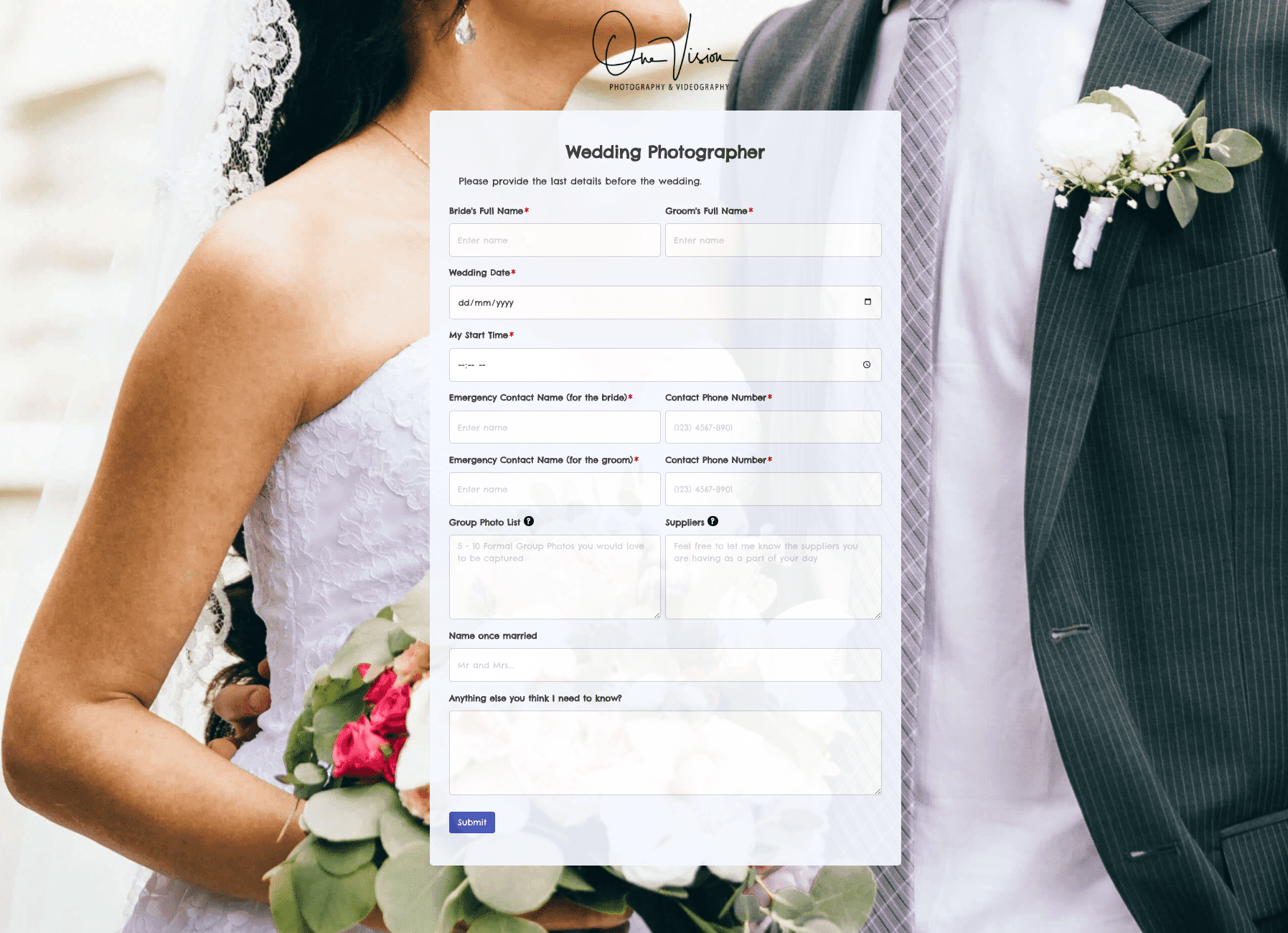 Wedding Photographer Form
Wedding Photographer Form
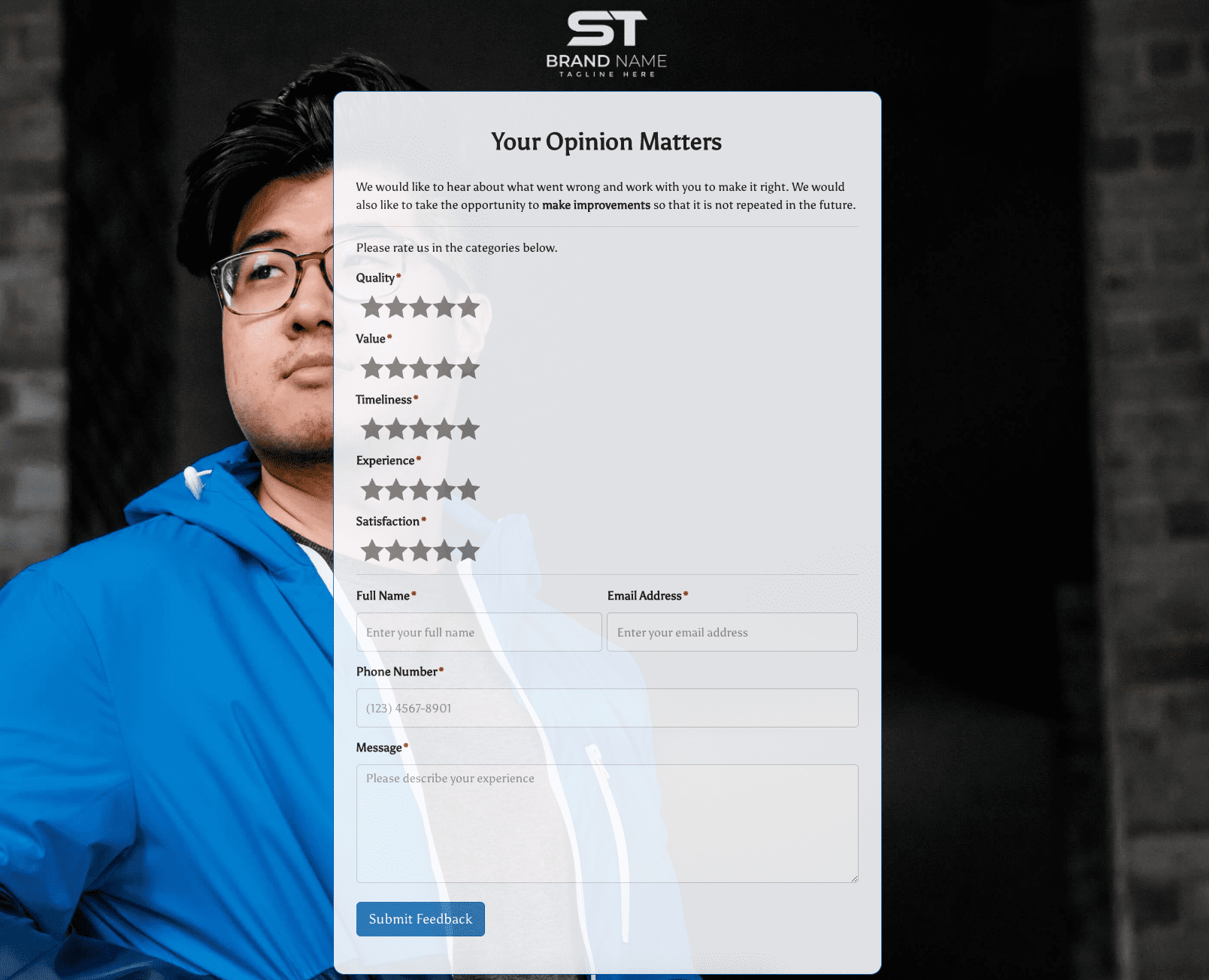 Your Opinion Matters Form
Your Opinion Matters Form



.jpg)